Hardening the production environment that runs your HashiCorp Vault clusters is one of the most important tasks you can do to secure the secret data managed by Vault. Our Learn guide on Production Hardening provides a number of invaluable recommendations, each of which add layers of defense in depth to help reduce the likelihood or impact of compromise.
Some of the Operating System specific recommendations include things like not running Vault as the root user and disabling core dumps. Another recommendation is to configure SELinux or AppArmor. SELinux and AppArmor are two methods to provide Mandatory Access Controls to processes running on Linux distributions. SELinux was originally developed by the United States National Security Agency (NSA), and since then has been included in Red Hat-based Linux Distributions, such as CentOS or Fedora. AppArmor, while very similar to SELinux, is supported by Canonical, and is therefore available on Ubuntu and related Linux Distributions.
To help operations staff implement this recommendation we’re happy to announce a baseline SELinux policy for securing Vault on Red Hat-based Linux Distributions. This will be initially available as an open source GitHub repo, and may eventually make its way to our Linux Repository too.
It is important that you test the SELinux policy out in your non-production environments before running it in production. While we have done baseline testing with CentOS and Fedora, your Vault environment is likely unique and will require modification to the policy.
One of the benefits of SELinux is that it is customizable to your particular security requirements, but with that flexibility comes complexity. To provide an initial, out-of-box experience, the current Targeted Policy is configured to label Vault files and folders as per those deployed if you install Vault using one of our Linux Packages.
»Getting Started
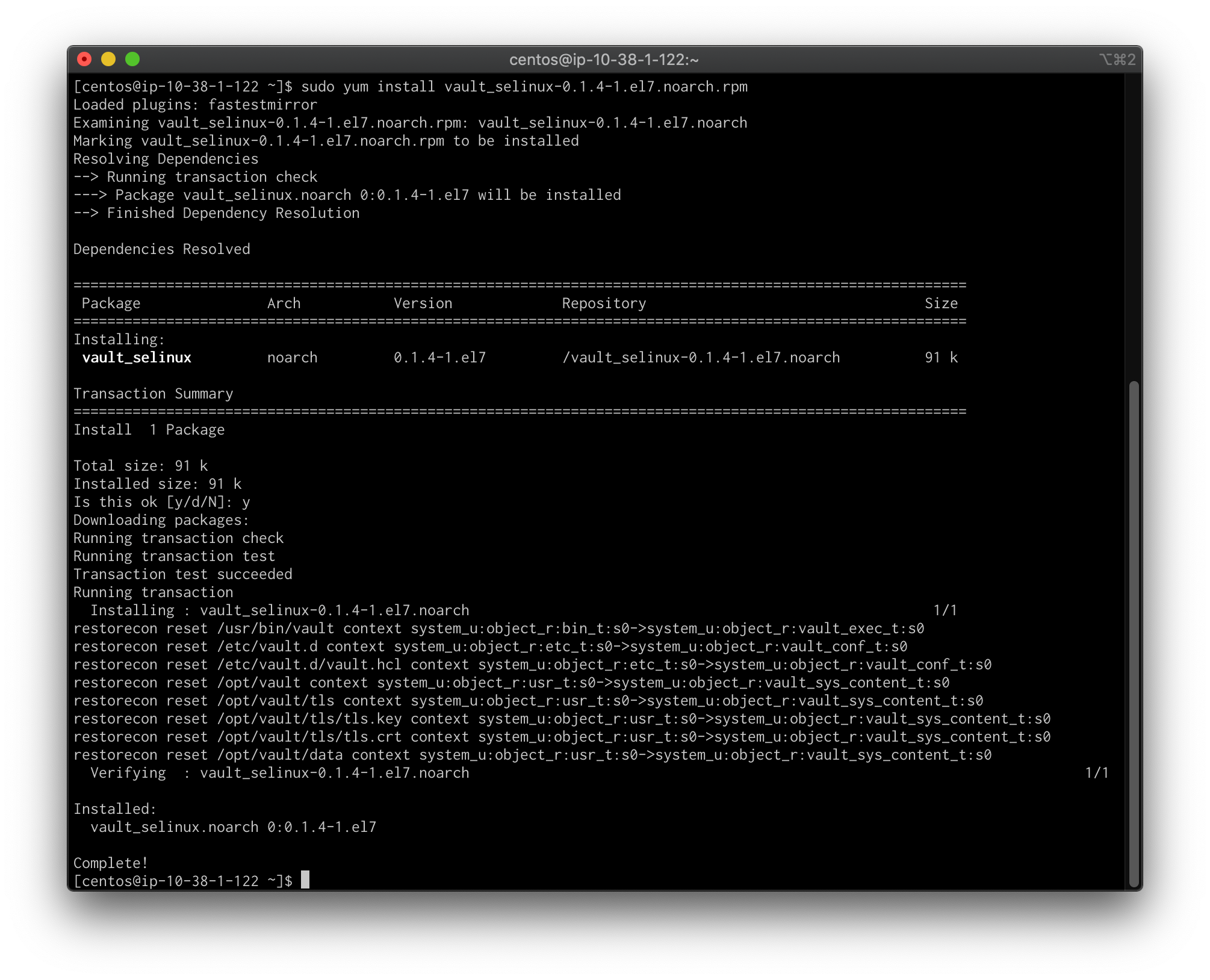
The easiest way to get started is to download and install one of the RPMs from our releases page. The el RPM files have been packaged and tested on CentOS 7 and 8, while the fc packages have been packaged and tested on Fedora 31, 32, and 33.
»Customized Policy
If you have a customized deployment of Vault then the packaged RPMs will not work. The best way to proceed is to clone the repo, then follow the steps under Testing Locally to install the policy.
After initial installation, the SELinux policy files that reside in products/vault_selinux may be edited and re-deployed by re-running the vault.sh script from within that same directory.
»Next Steps
Long-term we plan to make these RPMs available for installation from our official Linux repository. This will help streamline the process for operators that want to easily install Vault and the Vault SELinux Policy. We’re also going to investigate providing a similar policy for AppArmor for those practitioners running Vault on Ubuntu, Debian, and similar Linux Distributions. As always, we’re interested in community feedback.









