Injecting Vault Secrets Into Kubernetes Pods via a Sidecar
Watch this from-the-ground-up demo illustrating how to use Vault's newest method for managing secrets in a Kubernetes environment.
Speakers
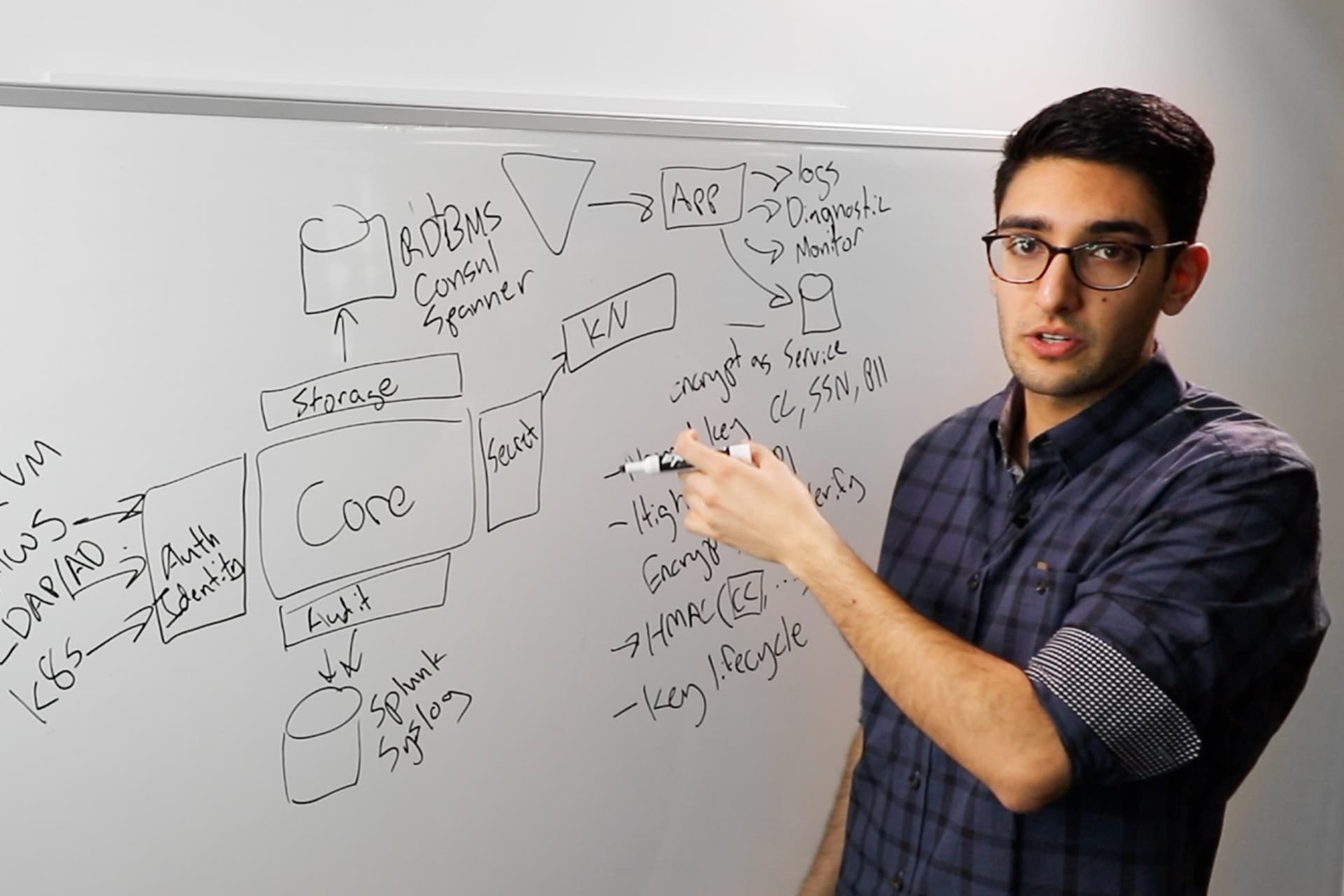
 Justin WeissigVault Technical Marketing, HashiCorp
Justin WeissigVault Technical Marketing, HashiCorp
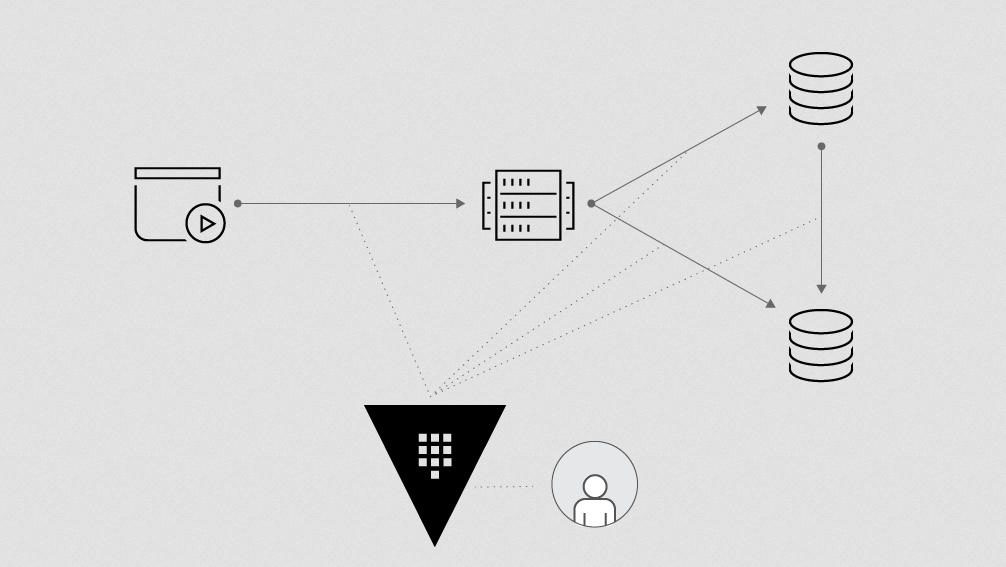
A new Kubernetes integration that allows applications with no Vault logic built-in to grab secrets out of Vault. This integration uses a new tool called vault-k8s that works with the Mutating Admission Webhook in Kubernetes to track and change specifically annotated pod configuration to allow secrets injection using init and Sidecar containers.
This means, no more managing tokens, connecting to an external API, or using any other mechanisms to have direct interaction with Vault.
In this demo, HashiCorp Technical Marketer for Vault Justin Weissig will walk through this process and discuss specific use cases, including:
- Init only container
- Init and Sidecar
- Pod authentication
- Flexible output formatting
Outline
0:00 — Why use Vault over Kubernetes Secrets?
6:10 — Demo: Setup
18:39 — Demo: Templating walkthrough
39:27 — Q&A
Slides
Q&A
If your Vault cluster is external, how do the pods authenticate to Vault to retrieve secrets?
Does the Helm chart work with Helm 3?
Who creates the
serviceaccount/tokenin the first place?We are using OpenShift and plan to install Vault on AWS, is there documentation for this scenario?
For the inject template annotation, is there a recomended way to use this feature within a Helm chart? It seems Helm would use the same syntax for templating. Is escaping required?
Can you use the templating with things like Helm?
Can secret data be appended to an existing file (instead of writing a new file)?
Will this amount to a lot of annotations for monolithic software we're putting into k8s that has to communicate with numerous APIs.
Is there any similar injection solution for docker-compose?