Why Consider Terraform Enterprise Over Open Source?
A consistent provisioning workflow with Terraform Enterprise means one workflow to learn, secure, govern, and audit.
Organizations adopt Terraform OSS to help provision and configure their infrastructure and cloud. Terraform Enterprise provides a central way for many users within the organization to safely and efficiently provision and manage their infrastructure.
However not every team has a business need for Terraform Enterprise immediately. We believe Terraform Enterprise provides increasing value to organizations as the complexity and size of their organization grow. The below information will help you determine when it makes sense to transition to a paid Terraform offering.
Many individuals and small teams adopt Terraform OSS to provision their clouds using infrastructure as code. As your teams expand, organizational challenges arise around collaboration, security, policy, and governance. Some questions you may need to answer include:
- How will provisioning workflows be impacted when moving from 1 individual to multiple team members?
- How will teams collaborate?
- How will teams create and manage infrastructure state?
- How can self-service infrastructure for developers be enabled?
- How do operators enforce provisioning rules and best practices within Terraform?
- How do administrators enforce role-based access control (RBAC) on each of the infrastructure teams? (e.g. Network, Database, Monitoring)
- How can a secure multi-cloud be enabled?
If some of these questions apply to your teams, consider learning more about Terraform Enterprise below.
What drives the most value in Terraform Enterprise?
The largest business benefits that our existing customers have seen from Terraform Enterprise relate to operational efficiency, controlling cloud costs and, reducing risk.
Operational efficiency
Operational efficiency is achieved through strong developer-operator team workflows integrated with workspaces, modules, and the Terraform Enterprise configuration designer. Terraform Enterprise provides a logical unit to break down infrastructure as code into workspaces.
A workspace is everything Terraform needs to run: a configuration file, input variables, and a statefile. Workspaces can convert monolithic infrastructure into modular infrastructure. They help reduce surface area and impact of errors to a single workspace and simplify debugging errors.
The private module registry and configuration designer allow users to leverage pre-built libraries of infrastructure. The combination of these can reduce configuration creation time for developers by up to 80%. Now, users only have to define values for their configuration variables (cloud credentials, region, # of resources), requiring less employee time and resources.
Modules can help further reduce the number of full-time employees per year that are dedicated to provisioning and managing a single vendor by leveraging the same team of individuals to provision and manage all vendors. Results can be seen for onboarding new vendors faster compared to learning cloud-native tools.
Risk reduction
Sentinel policy as code provides risk reduction by enforcing security, compliance and operational best practices for how resources can be consumed. It’s a powerful language framework built into all of HashiCorp's Enterprise products to enforce guardrails, business requirements, and legal compliance in real-time. With Sentinel and the private module registry, organizations can ensure that only the appropriate cloud resources are deployed in the way they are intended, following regulatory compliance to avoid fines, and prevent vulnerabilities and breaches.
Controlling cloud costs
Terraform Enterprise can help organizations systematically control costs by up to 30-40% using modules and Sentinel policies to enforce operational best practices. Sentinel can help ensure operational best practices are followed to prevent overspending on cloud costs. Sample policies to enforce include preventing overprovisioning, approval process for expensive resources used in dev/test, and spinning down resources after they’re no longer needed.
Additional details regarding the feature-specific benefits are outlined in the tables and diagram below.
Collaboration Capabilities
| Feature | Functionality | Benefits |
|---|---|---|
| Workspaces | Allow teams to map functional responsibilities to individual workspaces & link workspaces via APIs. | Teams work in-parallel, leverage other workspaces, errors contained to workspace. |
| Team Management | Administrative management to create separate 'orgs'. Create multiple teams and assign permissions. | Multi-tenancy for separate BU. Govern separate teams with correct permissions. |
| Private Module Registry | A central library of versioned & validated modules. | Pre-built sets of resources with best practices built-in; self-service model of infrastructure. |
| Configuration Designer | GUI-based workflow to select, combine, define variables and create unique workspaces. | Developers build configuration from pre-defined IaC modules; provision on-demand. |
| Remote Operations | Execute commands for TFE directly from the CLI (plan/apply). | Allows developers to use preferred workflows while still having the benefits of TFE. |
Governance and Policy Capabilities
| Feature | Functionality | Benefits |
|---|---|---|
| Sentinel | Create policies as code and enforce them on every provisioning run. | Eliminate provisioned resources that don't follow security, compliance, or operational policies. |
| SAML | SAML for SSO provides the ability to govern user access to your applications. | Determine read and write controls for all users; easily automate and manage user control in TFE GUI. |
| Audit | Track historical changes across all providers. | Associate changes with correlated workspaces to know who is doing what to the infrastructure. Reduce cloud costs ($10B is overpaid annually) by understanding what can be de-provisioned. |
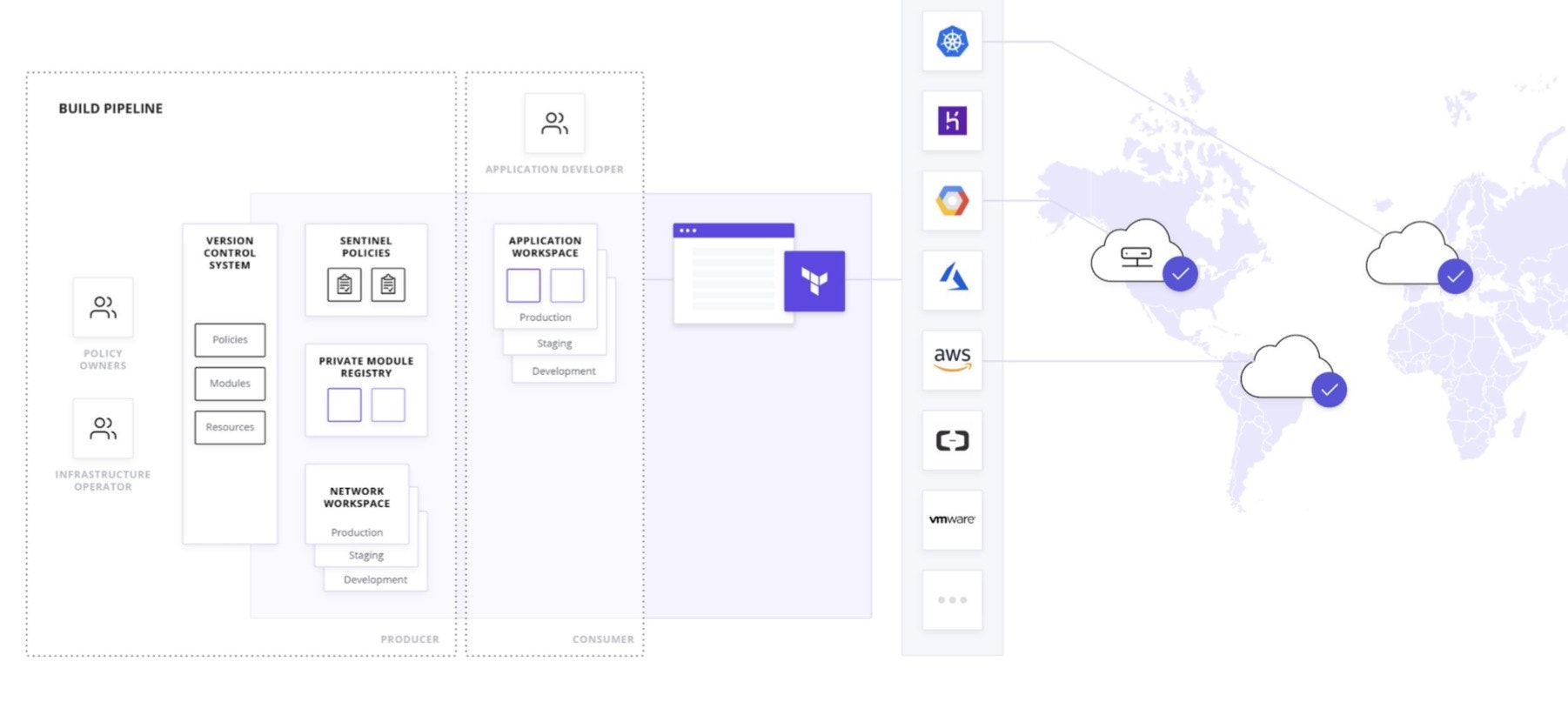
Terraform Enterprise Workflow Diagram
Why not build our own enterprise features on top of Terraform open source?
The core consideration for this question is opportunity cost. Should your engineers be working on reinventing something that infrastructure tooling specialists at HashiCorp have spent years researching and developing? Or should your teams be focused on building their own applications and creating revenue for your business?
Battle-tested, low-risk
You take on a much bigger risk when rolling out your own enterprise features. If a project of that magnitude doesn't pan out, you're left with significant sunk costs. In addition, consider the speed at which you can implement various provisioning capabilities if you buy Terraform Enterprise versus trying to build your own features from scratch. Rolling your own will always take longer—possibly years.
Maintenance costs
If you decide to build a forked version of Terraform, you'll either have to give up on receiving new features from the open source project or your developers will have to continuously maintain the compatibility between your version of Terraform and the official version.
Customer support
You'll also be giving up HashiCorp's ability to support your organization if you go too far down the DIY path with enterprise features. HashiCorp has an experienced group of Technical Account Managers and Support Engineers that have seen many different use cases for Terraform Enterprise.
By adopting HashiCorp's enterprise-ready solution, you reduce risk, and you'll also have a clear view of the product roadmap, which includes cost modeling and cascading runs.
A consistent provisioning workflow with Terraform Enterprise means one workflow to secure, govern, and audit. You’re able to consolidate provisioning by operating Terraform Enterprise as a centralized workflow and eliminate the provisioning of resources that do not follow policy for security, compliance, and operational best practices.
WHITEBOARD VIDEO: Why should I consider Terraform Enterprise?
Watch HashiCorp co-founder and CTO Armon Dadgar explain the challenges of using Terraform in a medium-to-large sized organization and how Terraform Enterprise helps make compliance, security, and provisioning workflows in those contexts much smoother.



