Note: HashiCorp Consul service mesh on Amazon ECS is now generally available and ready for production environments.
We are pleased to announce the public beta for HashiCorp Consul service mesh on Amazon Elastic Container Service (ECS). AWS users can now select Consul as their service mesh for secure ECS deployments.
In May 2021, we introduced Consul service mesh for Amazon ECS as a tech preview. Today’s beta release includes several new enhancements since the tech preview:
Secure deployment: Consul can now be deployed in secure mode, enabling defense-in-depth security mechanisms using access control lists (ACLs), Transport Layer Security (TLS), and gossip encryption. ACLs are used to provide secure access to Consul’s UI, API, CLI, service communications, and agent communications. Gossip communication between agents is secured and encrypted with a symmetric key, and TLS is used to secure the RPC calls between agents.
Support for Amazon ECS launch types: You can now deploy Consul client agents on both Fargate and EC2 launch types. The HashiCorp Consul AWS ECS Terraform module helps deploy applications seamlessly on both launch types.
HashiCorp Cloud Platform deployments: You can now deploy Consul client agents on ECS and peer these with Consul server agents on HashiCorp Cloud Platform (HCP).
Self-managed deployment on EC2 servers: You also have the option to deploy self-managed Consul server agents on EC2 instances and client agents on ECS instances.
»Deploying Consul Server(s) on HCP with Clients on ECS
Let’s take a look at how you can securely deploy Consul service mesh on ECS with a HCP Consul server cluster.
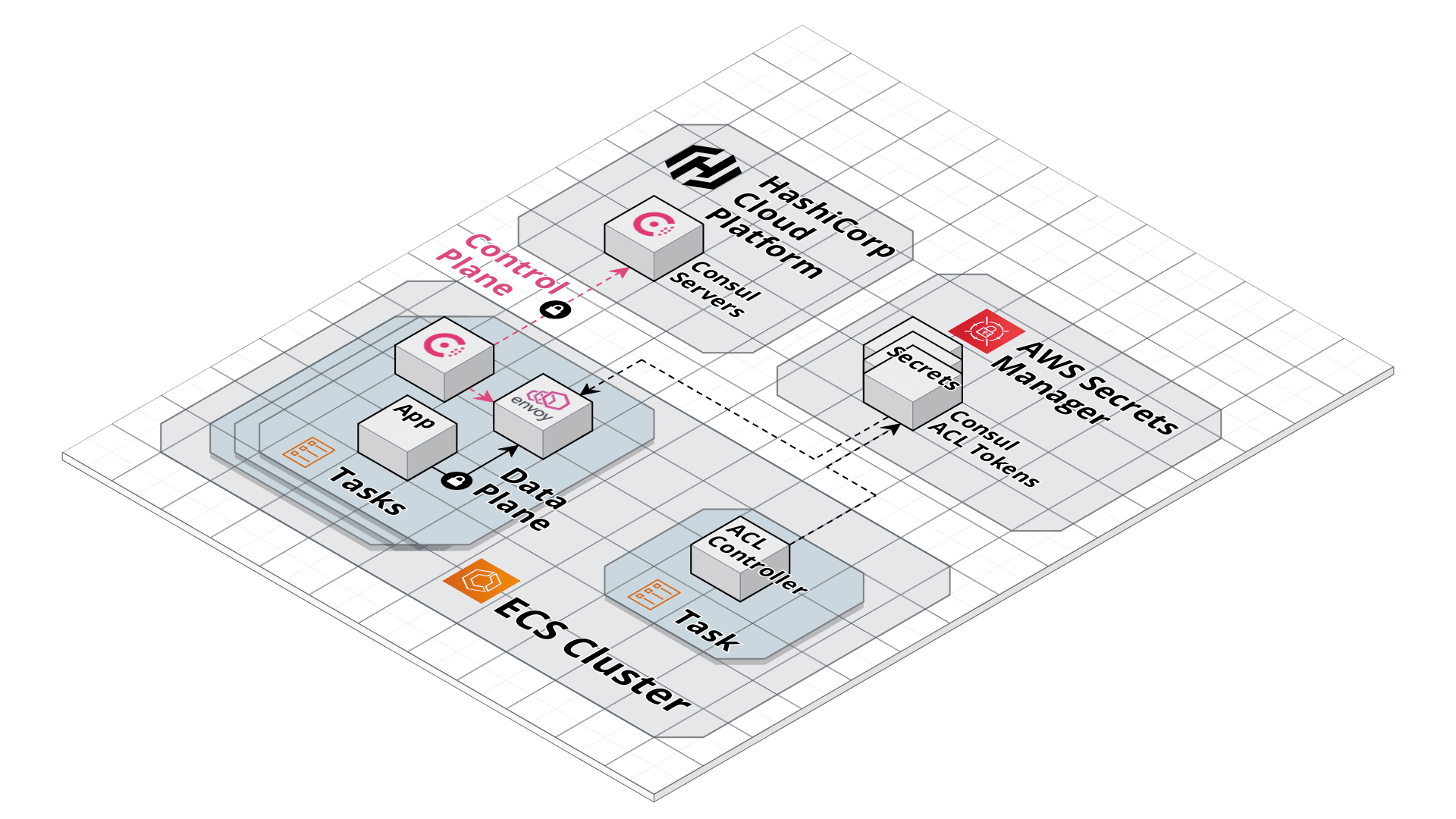
First, you need to create a HCP Consul server cluster. You can do so by following the Deploy HCP Consul with Terraform HashiCorp Learn guide. After completing the guide, you should have the server cluster running and the AWS peering between the HashiCorp Virtual Network (HVN) and your AWS VPC established.
Consul uses ACLs to securely communicate between agents and servers. Consul on ECS helps you automatically provision ACL tokens for the Consul clients and services on the service mesh using an ACL controller. The controller is an ECS task that runs in your ECS cluster. It watches for any new tasks that are coming up and creates ACL tokens with Consul. Here’s how to instantiate the ACL controller with Terraform:
module "acl_controller" {
source = "hashicorp/consul-ecs/aws//modules/acl-controller"
consul_bootstrap_token_secret_arn = aws_secretsmanager_secret.bootstrap_token.arn
consul_server_http_addr = hcp_consul_cluster.example_hcp.consul_public_endpoint_url
name_prefix = “example”
...
}
Now you can deploy a service using the mesh-task module with secure features enabled. To configure the mesh-task module, reference the needed credentials from AWS Secrets Manager and enable TLS and gossip encryption.
module "example_app" {
source = "hashicorp/consul-ecs/aws//modules/mesh-task"
family = "example-app"
container_definitions = ...
...
tls = true
consul_server_ca_cert_arn = aws_secretsmanager_secret.consul_ca_cert.arn
gossip_key_secret_arn = aws_secretsmanager_secret.gossip_key.arn
acls = true
consul_client_token_secret_arn = module.acl_controller.client_token_secret_arn
acl_secret_name_prefix = “example”
}
After the example-app task starts, the ACL controller will automatically create the ACL token for the service. Now the communication between the example-app task and the Consul cluster is secure.
»Learn More
For additional information about Consul on ECS, please visit our documentation and check out our HashiCorp Learn tutorial on how to get started with HCP Consul and ECS, which includes a sample application and code repository. HashiCorp Learn also offers many other HCP Consul related tutorials.
If you want to see live demos, here are some upcoming opportunities to see Consul on ECS in action and ask questions:
Webinar: How Comcast Runs Consul Service Mesh on Amazon ECS. Wednesday, October 6 at 9:30 a.m. PT
HashiConf Global 2021 (Tuesday - Wednesday, October 19-20):
Adopting Consul on ECS, Jaz Halford, Head of Cloud Engineering, Tide
Consul Use Cases At Stripe: Service Mesh and More, Ruoran Wang, Software Engineer, Stripe
»Try Consul on ECS Now
To get started deploying Consul on ECS via Terraform, use our Consul on ECS Terraform module.
As is typical with a beta release, we recommend against using this build in a production environment, but we encourage you to experiment with the new features in a controlled environment. We are eager to see how this support for ECS enhances your service mesh experience. If you encounter an issue, please file a new bug report in GitHub and we'll take a look.