Earlier this year, during HashiConf Europe’s day one keynote, we previewed a new feature — the addition of HashiCorp Sentinel policies to the Terraform Registry. Sentinel policies are now part of the HashiCorp Terraform ecosystem, so you can look to the Terraform Registry to start your policy as code journey. Partners and community members with policies to share can publish them to the wider open source community, while those in need of example or best-practice policies can search the Registry.
Let’s take a closer look at Sentinel policies in the Registry, and what it means for the Sentinel community.
»What Is Sentinel Policy?
HashiCorp Terraform provides cloud infrastructure automation with infrastructure and policies as code. Policy as code is becoming a popular approach to embedding automation-based guardrails into provisioning workflows, turning manual checks and governance into an automatic process that removes bottlenecks. Terraform uses Sentinel policy as code to embed these policies into workflows.
»Search for Policies in the Registry
Getting started using Sentinel is now as easy as searching for policies in the Terraform Registry. You can browse policies to get started, filtering by provider and category. The first policy libraries available as of this release include all HashiCorp Terraform foundational policies.
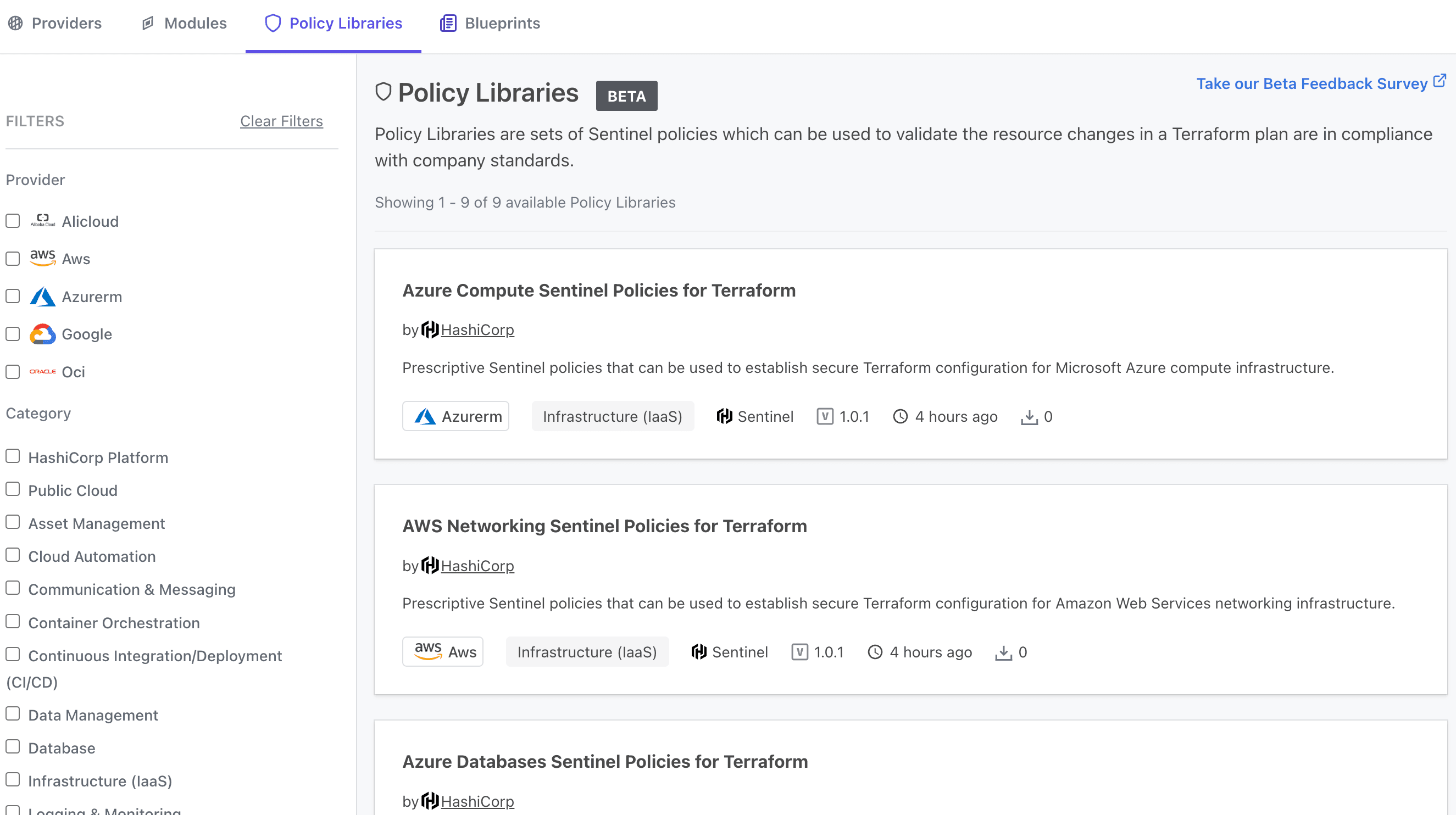
Policy libraries view with category and provider filters in the sidebar.
»Browse Policy Libraries
From this screen you can select a policy library, choose the policies that you want to use, and copy the code to add it to your Terraform Cloud workspace configuration. The Constructing a policy set section of our Managing Sentinel Policies tutorial walks you through how to do this.
If the policy is the start of a new policy set, create a sentinel.hcl file for the policy in a VCS-backed repo. If you already have a fitting policy set, add the policy code to the set’s sentinel.hcl file.
»Publish Policies to the Terraform Registry
Similar to Terraform providers and modules, public policy libraries are linked to a GitHub repository. A policy library contains one or more policies related by category.
Publishing a policy library is similar to publishing a Terraform module. Log into the Terraform Registry using your GitHub account, then navigate to Publish > Policy. From there you can select the GitHub repo that contains your policies and assign a category and providers, as shown here:
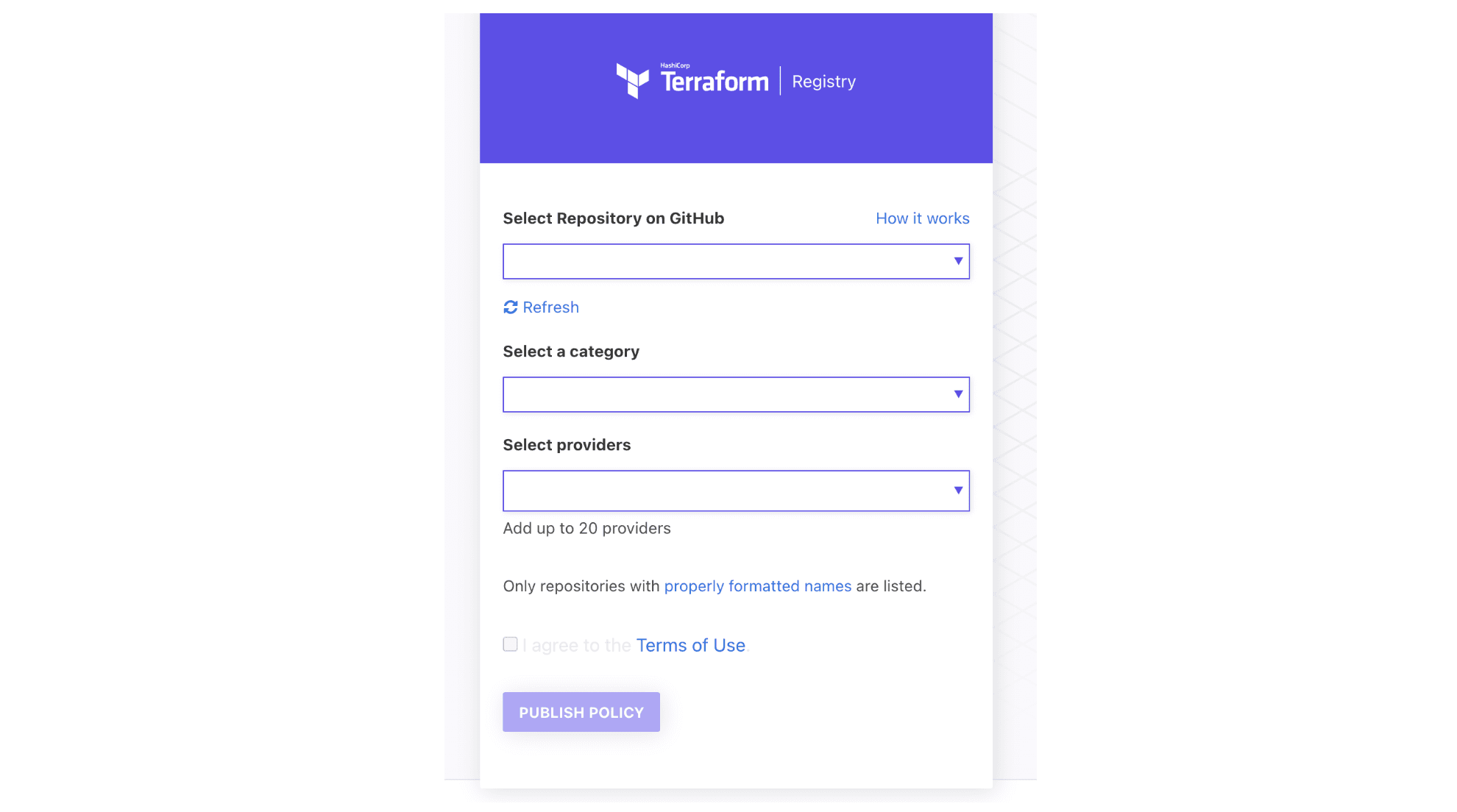
The documentation you’ve included for the policy library will display in the Registry when a user selects that policy, much like it does for a module. This is your chance to describe the intended uses for the policy and any relevant information about your organization.
Upon publishing, the Registry extracts information about the policy library from the policy library’s source. The policy library name, provider, documentation, and dependencies are all parsed and available via the UI or API, along with the same information for any policies in the policy library’s source repository.
For detailed publishing instructions, see Publishing Policy Libraries in the Terraform documentation.
»Learn More
We are thankful to our community members for their contributions to the HashiCorp Terraform Registry, and encourage Terraform users to publish policies to the Registry as we continue to build out the Terraform ecosystem. Check out the Terraform Registry here.
To learn more about using Terraform with Sentinel, check out the Terraform tutorials in HashiCorp Learn. For more information on Terraform Cloud and Terraform Enterprise, visit the Terraform product page. To get started today, sign up for a Terraform Cloud account.










