In March 2023, we announced the general availability of dynamic provider credentials in HashiCorp Terraform Cloud. This feature automates the creation of short-lived credentials for the officially supported cloud providers (Amazon Web Services, Microsoft Azure, and Google Cloud) and the HashiCorp Vault provider. Initially, the Vault integration supported only static secrets engines for use within Terraform configurations. Today, we’re excited to announce Vault-backed dynamic credentials, a native integration between Terraform Cloud dynamic provider credentials and the Vault dynamic secrets engines for AWS, Azure, and Google Cloud.
Vault-backed dynamic credentials represent a significant enhancement for our many customers already using Vault for on-demand cloud access and for any organization seeking to reduce the risks of managing credentials. HashiCorp Vault is a centralized identity-based management system for all types of secrets. Unifying these two capabilities provides a seamless approach for securing your cloud provisioning workflows.
»Better together
Dynamic provider credentials in Terraform Cloud eliminates the risks associated with storing long-lived credentials and avoids the operational burdens of manually rotating them.
Vault-backed dynamic credentials in Terraform Cloud combines dynamic provider credentials with Vault secrets engines to offer a consolidated workflow. This approach authenticates Terraform runs to Vault using workload identity tokens generated by Terraform Cloud, then uses Vault secrets engines to generate dynamic credentials for the AWS, Azure, and Google Cloud providers.
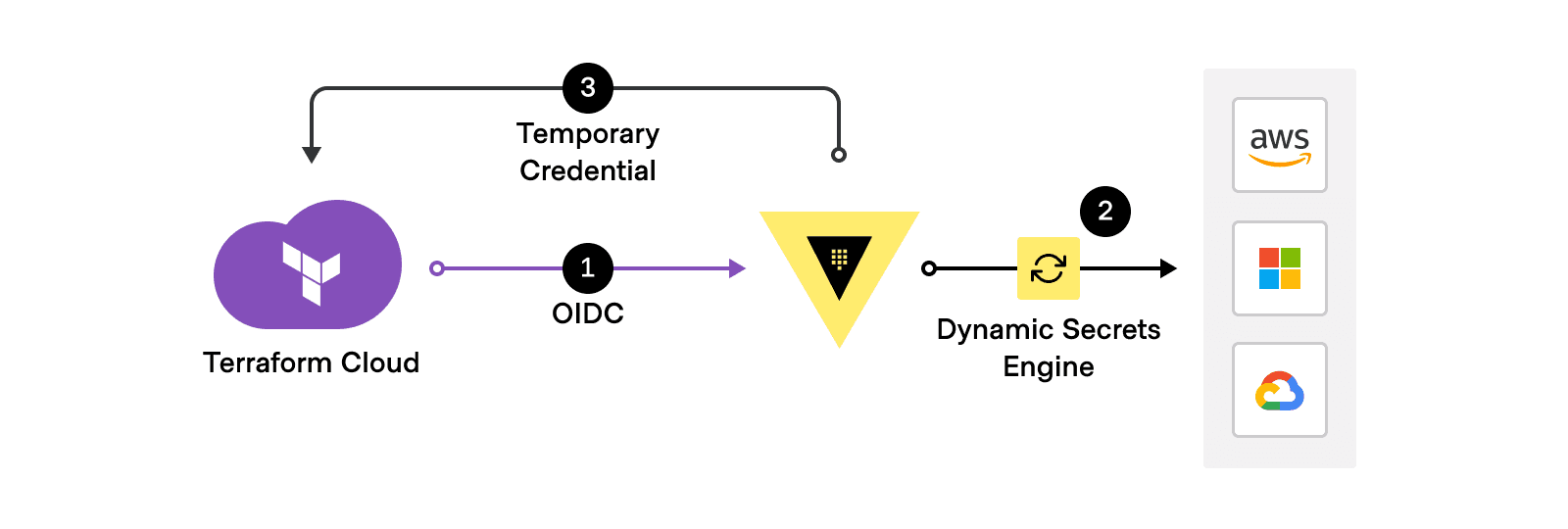
Vault-backed dynamic credentials authenticates to Vault with OIDC, then uses Vault secrets engines to generate cloud credentials for Terraform Cloud runs.
First, Terraform Cloud runs are authenticated to Vault with industry-standard OpenID Connect (OIDC) workload identity tokens, using Vault’s JWT/OIDC auth method. Then, Vault uses the configured dynamic secrets engine for AWS, Azure, or Google Cloud to generate a short-lived cloud credential that is unique to the Terraform run phase. This credential is injected into the run environment for use with the corresponding Terraform provider. Once the plan or apply is complete, the temporary Vault token and downstream credential are revoked, eliminating the risk of re-use.
The advantages of this approach include:
Consolidated management and auditing for all your cloud credentials and other secrets
No OIDC setup required in your cloud provider
Leverage your existing Vault secrets engine configurations
No need to expose inbound access to self-hosted Terraform Enterprise instances from cloud providers to validate OIDC metadata
»Setting up Vault-backed dynamic credentials
At a high level, setting up Vault-backed dynamic credentials involves three steps:
Performing the setup for dynamic credentials with the Vault provider.
Configuring the appropriate secrets engine in Vault: AWS, Azure, or Google Cloud.
Adding additional environment variables to your Terraform Cloud configuration based on the Vault secrets engine used. This can be done via workspace-level variables or by using variable sets at the workspace or project level.
This feature automatically injects the temporary cloud credential into the Terraform Cloud agent runtime environment, eliminating the need to configure the corresponding Vault data source in your Terraform code.
»Next steps
Vault-backed dynamic credentials enhances the existing Terraform Cloud dynamic provider credentials feature by allowing you to consolidate onto a unified secrets management platform and workflow. Learn more with the dynamic provider credentials documentation and hands-on tutorial: Authenticate providers with Vault-backed dynamic credentials.
Get started with Terraform Cloud for free and try HCP Vault, the easiest way to get started with Vault. You can link your Terraform Cloud and HashiCorp Cloud Platform (HCP) accounts together for a seamless sign-in experience.









