If you are not familiar with HashiCorp Configuration Language (HCL) or prefer other programming languages when using HashiCorp Terraform, CDK for Terraform (CDKTF), released in GA last August, lets you define and provision cloud infrastructure using your choice of language (includingTypeScript, Python, C#, Java, and Go), while still benefiting from the full ecosystem of Terraform providers and modules. But until now, there was no easy way to discover examples of resource configurations in your preferred language without doing your own mental translation.
Today, we are excited to announce CDK for Terraform multi-language provider docs in the Terraform Registry. This helps you simplify infrastructure provisioning and improve productivity by offering provider configuration options and code samples for the programming languages supported by CDKTF alongside the HCL documentation in the registry.
If you are new to working with a particular resource in your preferred programming language, such as TypeScript, for example, you can copy-paste the code samples from the multi-language provider docs in the registry and then adapt them for your needs. This is especially useful when starting a new project — no mental translation required.
An introduction to the CDK for Terraform multi-language provider docs
We are launching this feature with the following set of providers and resources and plan to gradually expand the documentation over time:
Amazon Web Services (AWS) provider documentation (available in TypeScript and Python)
Services: EC2, Lambda, VPC, and EKS
Terraform Cloud/Enterprise provider documentation (available in TypeScript and Python)
To view the new documentation, navigate to the Terraform Registry and then to the particular resource page you want to provision in your CDKTF project. For example, if you’d want to provision an Amazon EC2 Dedicated Host in TypeScript, you can now find the translated snippet in the Registry by selecting “TypeScript” in the language selection dropdown.
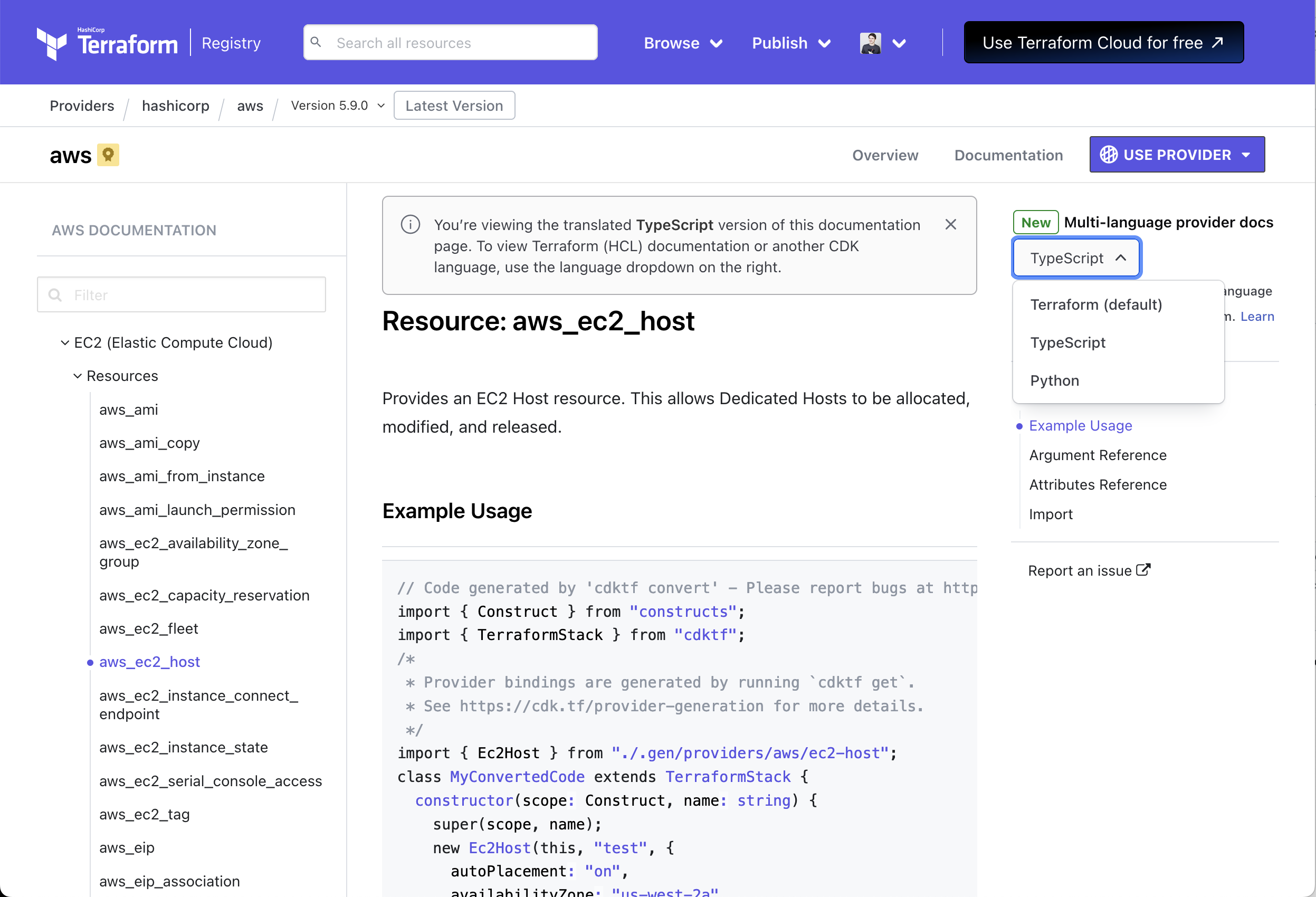
Terraform multi-language provider docs provide code samples in TypeScript and Python.
»Try CDK for Terraform
CDKTF is designed to help make Terraform adoption easier so more developers will enjoy the benefits that Terraform provides — cost savings, faster delivery, and reduced risk. The new multi-language provider docs are another major step toward that goal.
If you’re new to the project, these tutorials for CDK for Terraform are the best way to get started. You can dive deeper into our documentation with this overview of CDKTF.
Whether you’re still experimenting or actively using CDK for Terraform, we’d love to hear from you. Please file any bugs you encounter, let us know about your feature requests, and share your questions, thoughts, and experiences in the CDK for Terraform discussion forum.








