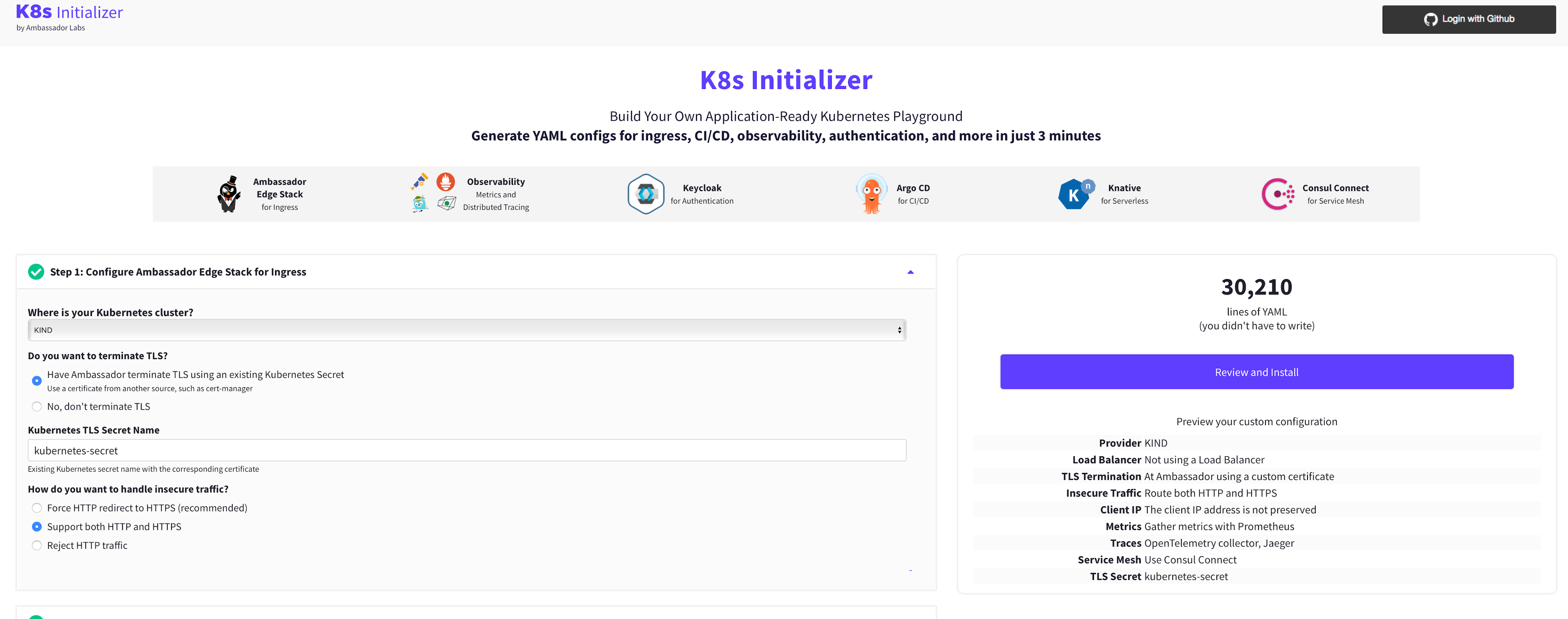
HashiCorp Consul integrates with Ambassador to securely route ingress traffic into Consul service mesh when using Kubernetes. When onboarding applications onto a service mesh or when integrating with existing applications outside of the mesh, a north-south API gateway is typically required for communications with clients outside of the network. Ambassador is a Kubernetes API Gateway that allows you to route incoming traffic to your Consul service mesh proxies while also providing the ability to leverage advanced API Gateway functionalities such as rate limiting and authentication. In this blog post, we describe a new way to get started with both Ambassador and Consul service mesh using the Kubernetes Initializer built by Ambassador.
»Overview
Kubernetes Initializer is a tool built by Ambassador Labs that allows you to quickly deploy a sandbox environment of Ambassador along with other platforms such as Prometheus and Consul. Using Kubernetes Initializer you can deploy both Ambassador and Consul across various different Kubernetes distributions such as AKS, EKS, GKE, Minikube, and kind.
»Getting Started
In this example let us walk through setting up Ambassador, Jaeger, Prometheus, and Consul together. First, let’s take a look at how the K8s Initializer can quickly provide a deployment descriptor for both Ambassador, Consul, Prometheus, and Jaeger.
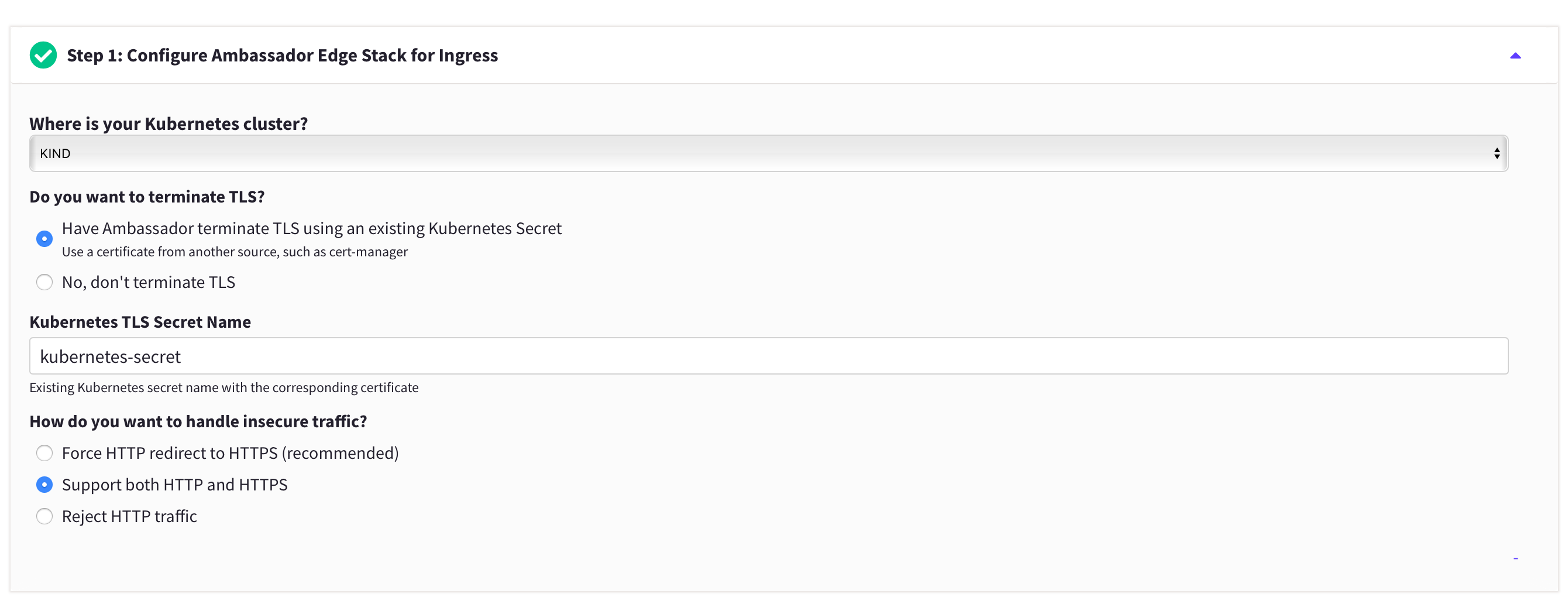
The Kubernetes Initializer provides a quick way to select your desired infrastructure and specify how you would like to handle insecure traffic that enters your Kubernetes cluster. For Cloud Service Provider distributions of Kubernetes, the initializer also generates YAML to create a LoadBalancer using a load balancer type of your choosing (Layer 4 or Layer 7). We can also select kind for local installations which are perfect for sandbox environments.
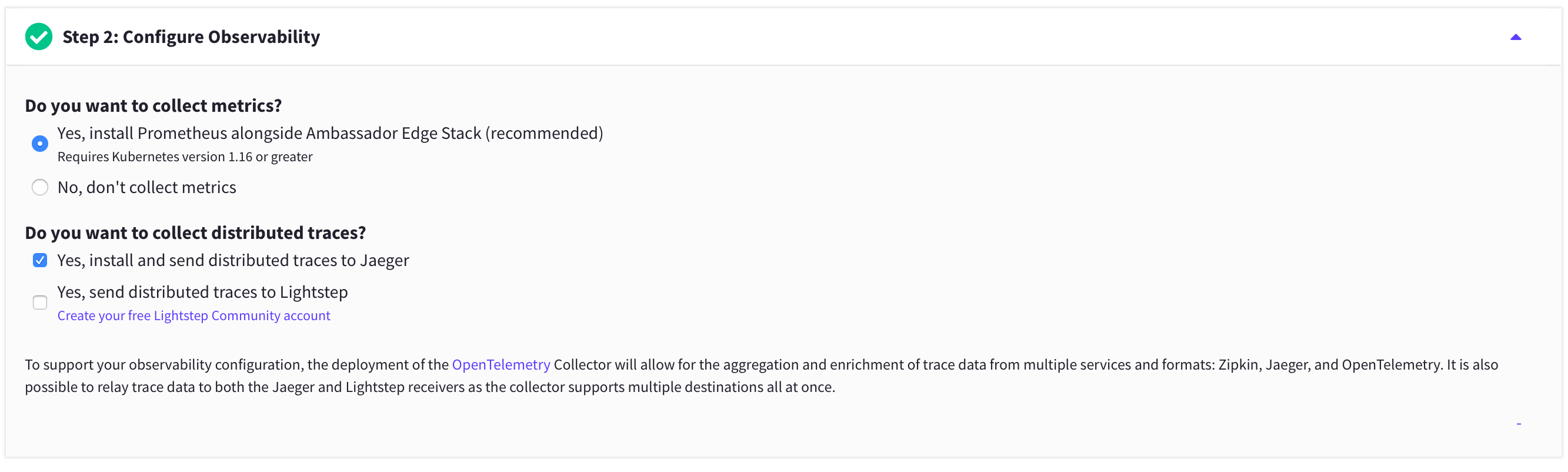
In addition, you can go setup Observability so that we can easily collect metrics via a Prometheus backend for both Consul and Ambassador. As part of the configuration, the initializer can also configure Consul to collect distributed traces to an installation of Jaeger that is deployed via the initializer YAML.
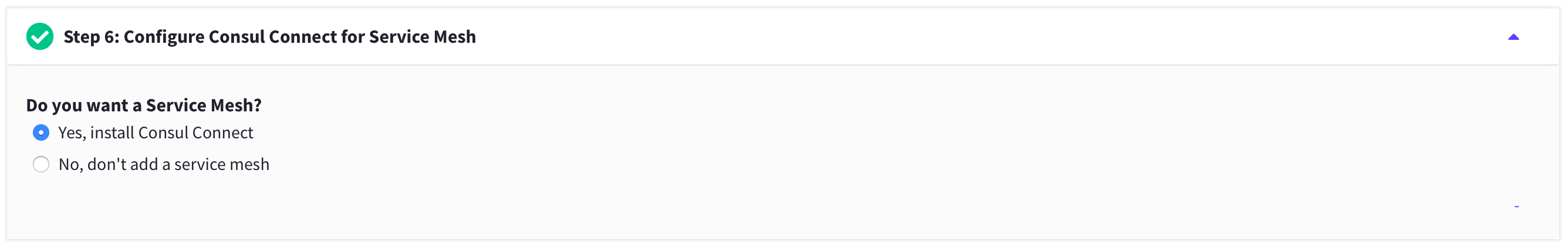
Finally, you can select Consul as the service mesh to integrate with Ambassador to easily deploy Consul with Ambassador via the YAML generated by Kubernetes Initializer.
»Conclusion
Please join us for an upcoming webinar to get a deep dive on how to use Consul Kubernetes and Ambassador together with Kubernetes Initializer. For more information on how to deploy Consul in production with Ambassador please visit the documentation we have available to describe the Ambassador integration with Consul.









