HashiCorp Vault 1.8 was released on July 28th, introducing some exciting new features and enhancements. Now you can visit the Vault 1.8 Release Highlights collection on HashiCorp Learn and start exploring what's new.
»Install a HashiCorp Enterprise License
Starting with Vault 1.8, Vault Enterprise autoloads the license as the server starts up. This is a significant change in behavior. The Install a HashiCorp Enterprise License tutorial demonstrates how to autoload the license.
Choose the Vault tab to learn how to specify the license.
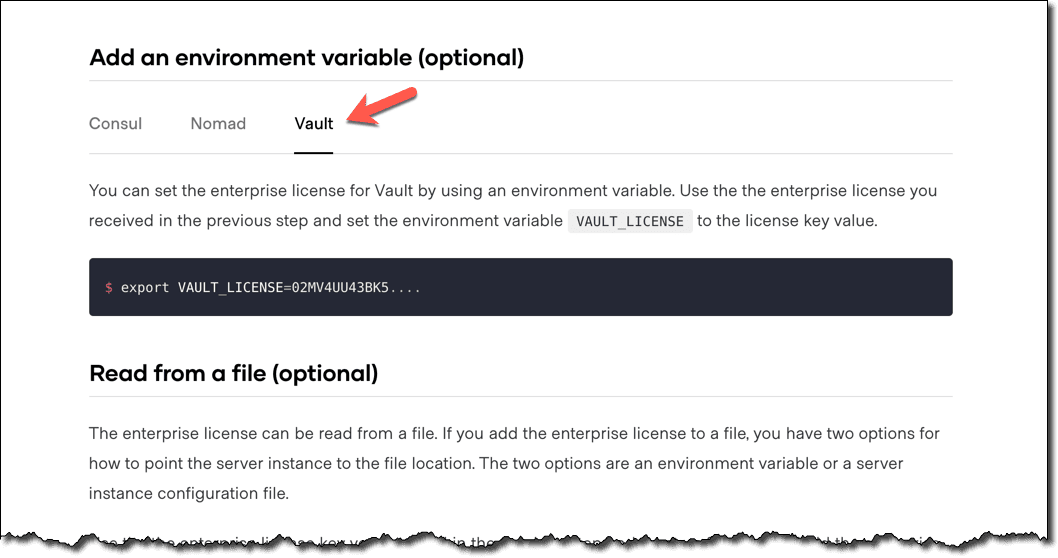
Also, see the Frequently Asked Questions (FAQ) documentation which answers common questions about this change.
»Control Groups
Vault Enterprise control groups enforce additional authorization factors before satisfying a client request. For example, when an authorized user requests to read EU customer data, at least two account manager approvals are required.
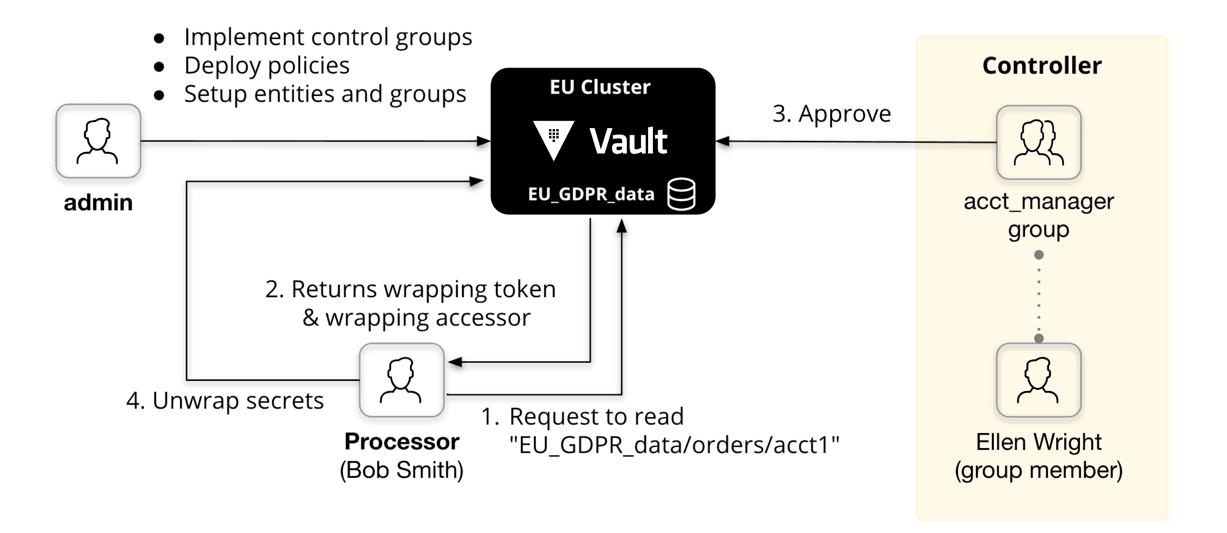
Previously, control groups defined those conditions on the target path regardless of the request type. Vault 1.8 extended this feature so that you can narrow the scope of the control group to the capabilities level.
If you are new to control groups, read through the entire Control Groups tutorial. Otherwise, skip to the Define a Control Group for Operations section to learn about these new enhancements.
»Troubleshoot Irrevocable Leases
Vault 1.8 introduced enhanced expiration manager functionality to internally mark leases as irrevocable after 6 failed revoke attempts, and stops attempting to revoke them. This prevents Vault servers from trying to revoke all expired leases at once during startup.
The Troubleshoot Irrevocable Leases tutorial demonstrates these improvements.
»Diagnose Server Issues
When Vault server fails to start, the Vault operators have to troubleshoot the server configuration.
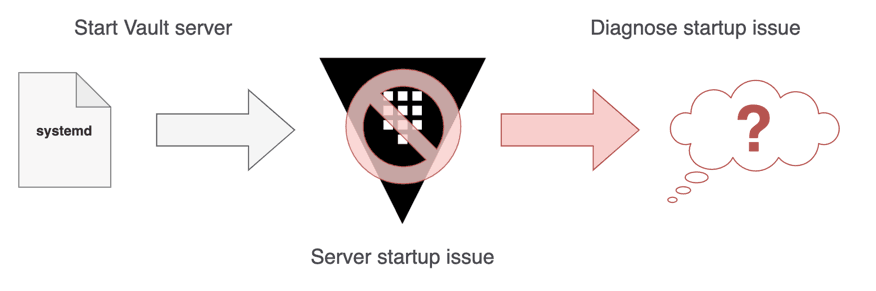
To help the Vault operators, Vault 1.8 introduced the vault operator diagnose command.
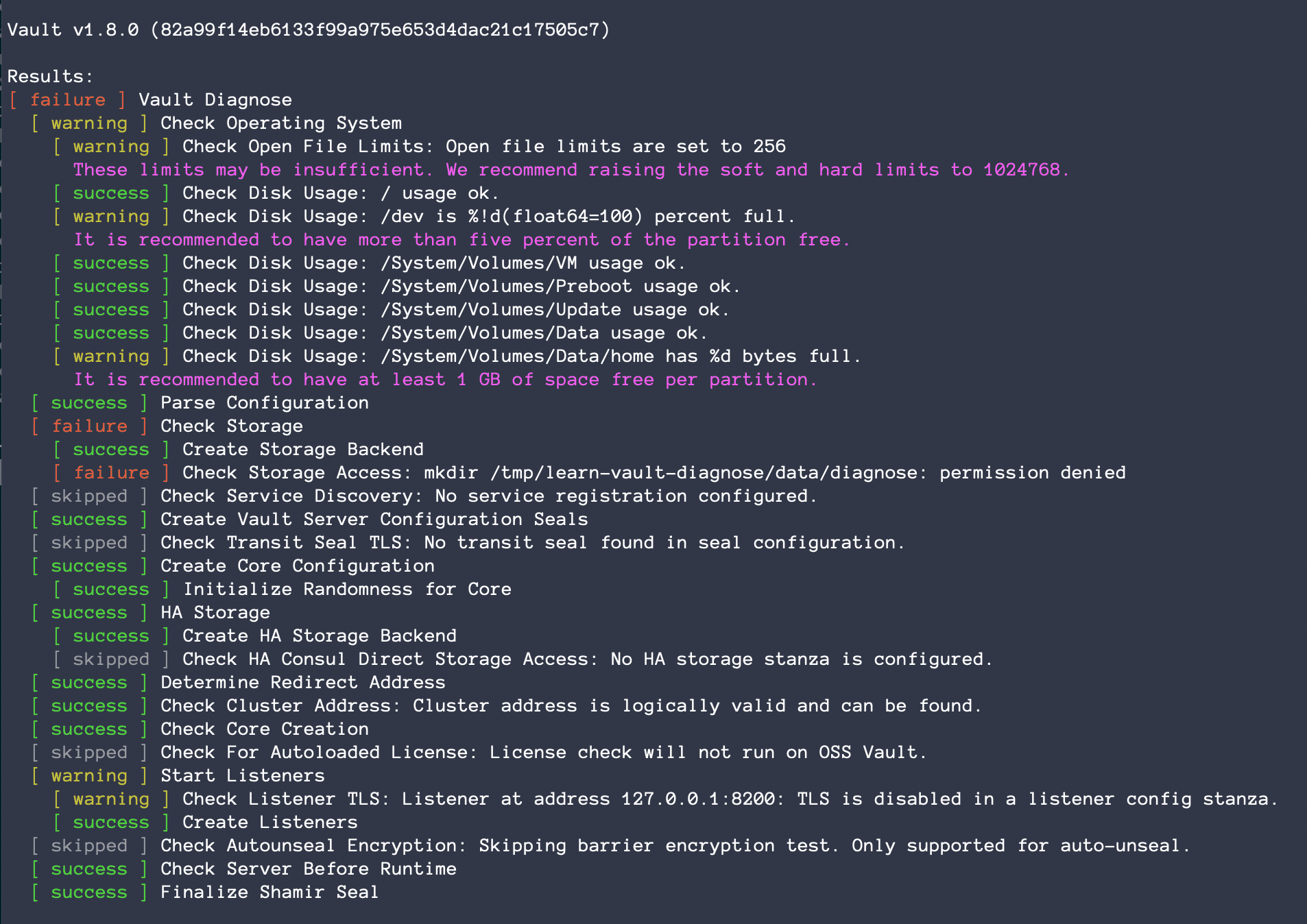
If you are responsible for configuring and starting up a Vault server, check out the Diagnose Server Issues tutorial.
»Inspect Data in BoltDB
When using Vault Integrated Storage as the storage backend, the cluster persists all encrypted data to a bbolt key/value store. The Inspecting Data in Integrated Storage tutorial walks through the Vault API to inspect data.
The Inspect Data in BoltDB tutorial demonstrates how to access low-level details from the database file when a Vault cluster is not operable.
»Next Steps
Visit the Vault 1.8 Release Highlights collection on HashiCorp Learn to see all of the tutorials mentioned here, and visit the Vault homepage on HashiCorp Learn for all of the latest updates on new tutorials and collections.







