Today we’re announcing the release of HashiCorp Boundary 0.5 and Boundary Desktop 1.2.1. This latest release includes a new event-logging system for operators to gain more fine-grained visibility into running Boundary clusters, CRUD capabilities for credential stores and credential libraries in the administrative console, and enhancements to session cleanup.
»Event Logging
Boundary’s new event logging system is a milestone on our observability roadmap, giving operators greater visibility into system information in a well-defined, structured format. When enabled, event logs are the only type of logging Boundary performs, meaning standard system information and debug logs will no longer appear in stdout.
The new structured event logs are filterable by event type and other expressions that users define. Because event logging is a big change to our product, we are also still supporting our legacy HCLog output through a user-configurable setting.
For more about event logging usage, see our documentation.
»Credential CRUD for Administrative Console
In 0.4, we released the Vault integration for credential brokering, allowing operators to configure Vault integration via the CLI. The 0.5 release enables administration to configure these resources through the administrative console.
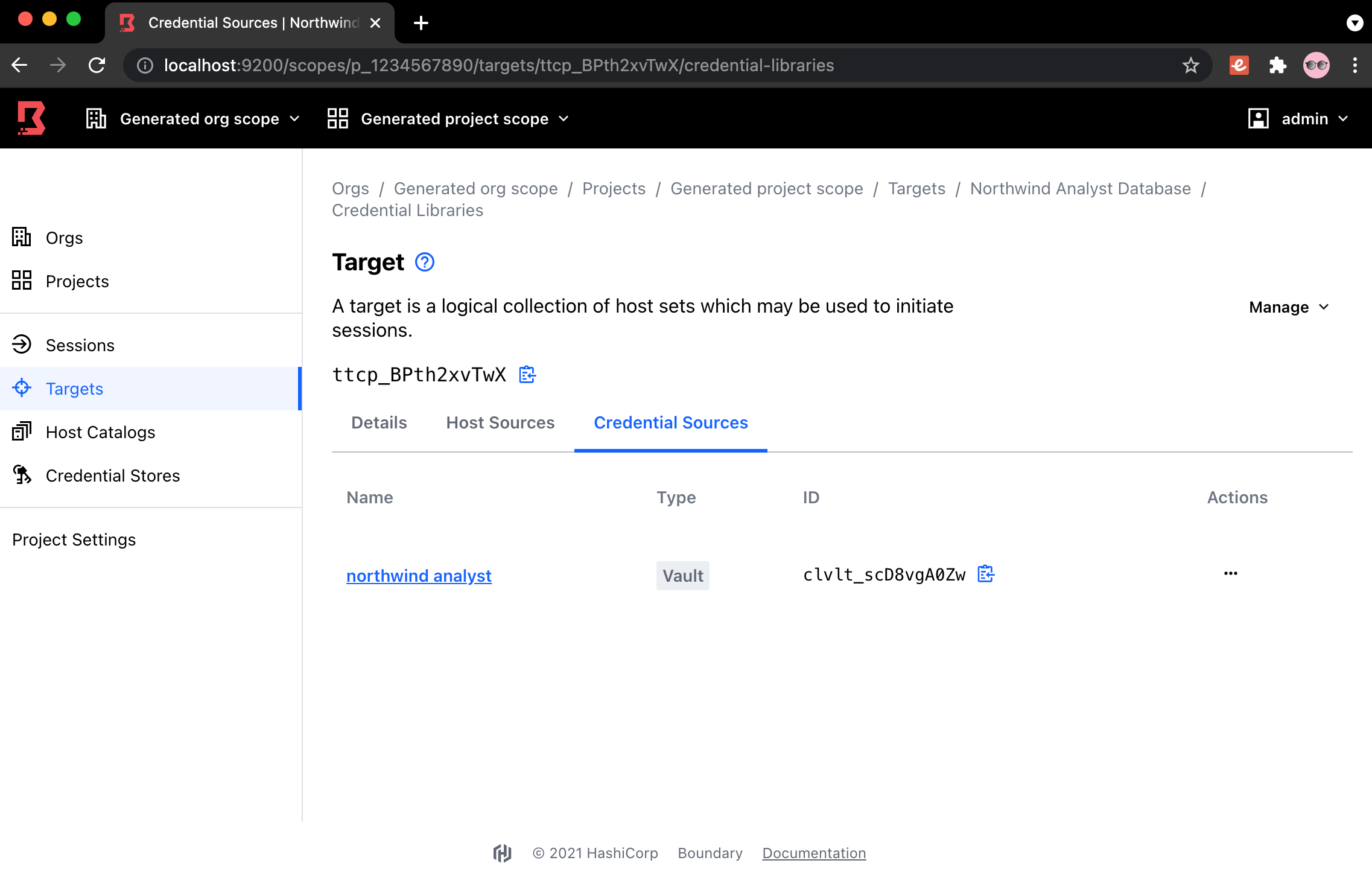
Configuring Vault Integration for a Boundary Target.
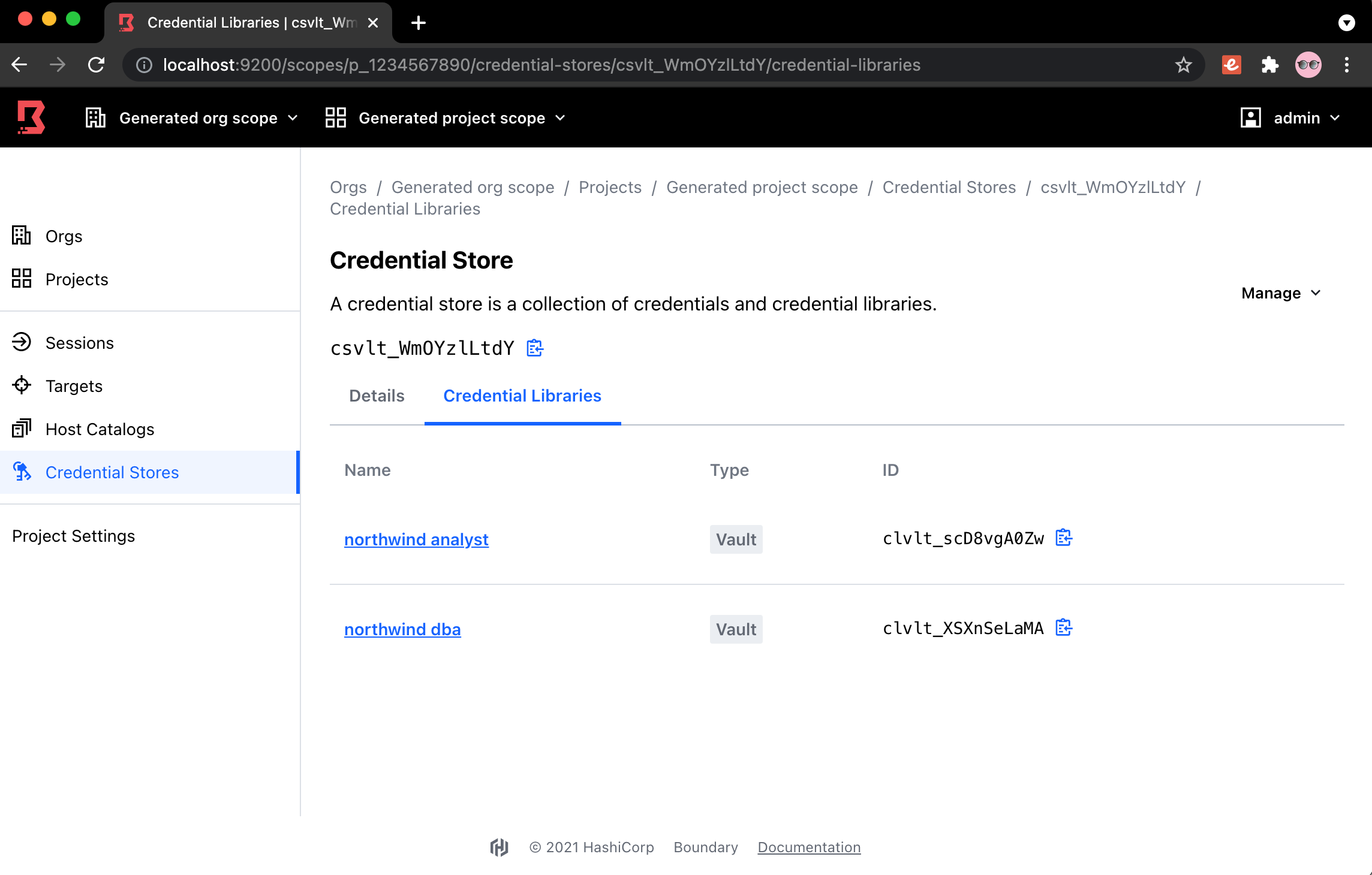
Establishing Credential Stores via Vault.
»Upgrade Details
Boundary 0.5 introduces significant new functionality and is available for download now. Please review Boundary’s general upgrade guide and Release Notes for details.
As always, we recommend upgrading and testing this release in an isolated environment. If you experience any issues, please report them on the Boundary GitHub issue tracker or post to the Boundary discussion forum. As a reminder, if you believe you have found a security issue in Boundary, please responsibly disclose it by emailing security@hashicorp.com — do not use the public issue tracker. Our security policy and our PGP key can be found on the HashiCorp security page.









