CDK for Terraform (CDKTF) lets you write Terraform configurations in your choice of TypeScript, Python, C#, Java, or Go, and still benefit from the full ecosystem of HashiCorp Terraform providers and modules. CDKTF was first released in GA in August, 2022.
Today, we’re releasing CDKTF 0.15, which introduces several improvements that make the Cloud Development Kit (CDK) easier to use with Terraform Cloud or Terraform Enterprise, including:
Improvements to the
cdktf diff,cdktf apply, andcdktf destroycommands: Now you can view the complete plan while running the command on Terraform Cloud and Enterprise.Automatic creation of Terraform workspaces: Automatically create a workspace when you add a Terraform stack to an application and run
planandapply.Improve parity with Terraform Cloud/Enterprise: Switching from an API-based implementation to the Terraform CLI enables a similar experience with both Terraform Cloud and Terraform Enterprise.
»Improvements to the CDKTF Plan and Apply Commands
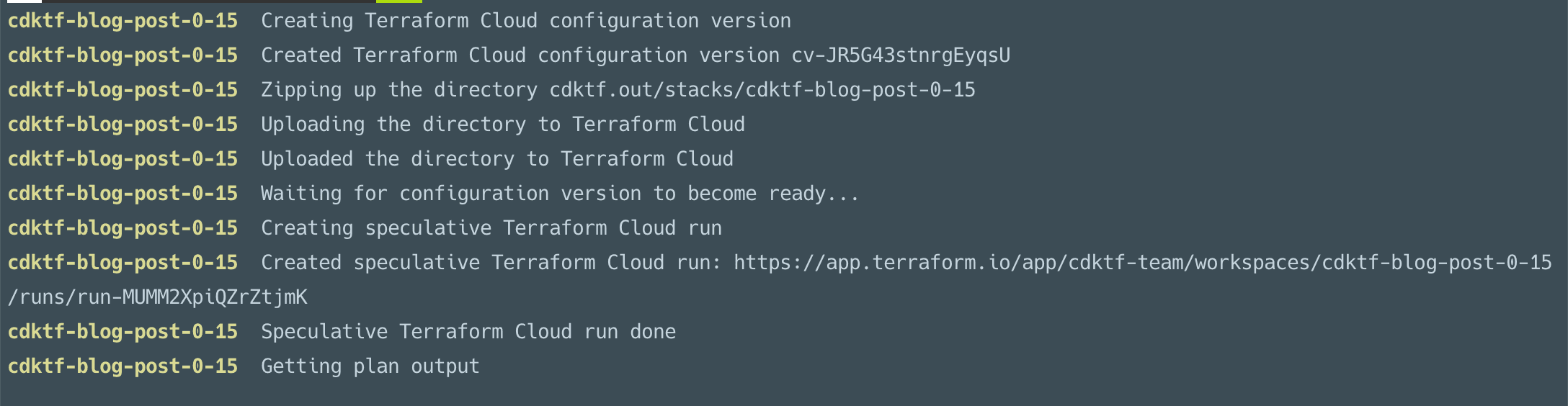
Prior to the 0.15 release, when your CDKTF stack was configured to use Terraform Cloud or Terraform Enterprise as a backend, the interaction with Terraform inside of Terraform Cloud was hidden from you. As you can see in this screenshot, you could follow your run in the Terraform Cloud or Terraform Enterprise UI only through a URL:
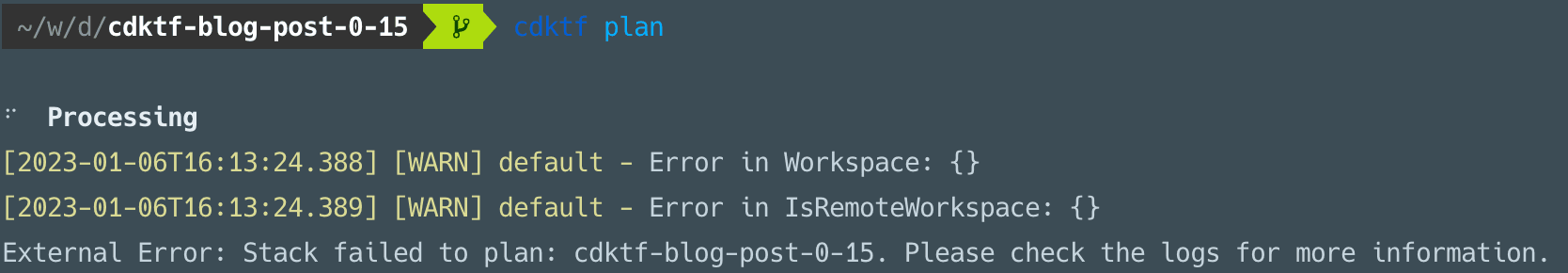
This adds an extra step to the development process. Showing that information while the commands execute would make the experience seamless. So with CDKTF 0.15, we switched out the way CDKTF interacts with Terraform Cloud. We replaced the Terraform Cloud API-based implementation with calls to the Terraform CLI itself. This allows us to show the plan with all the details Terraform provides:
This means that CDKTF now supports cost estimations, Sentinel policies, and all the Terraform Cloud/Enterprise setups that Terraform supports.
»Automatic Creation of Terraform Workspaces
If you’re already familiar with CDKTF, you might have noticed that CDKTF applications often host multiple Terraform stacks, this is even a recommended best practice. Each stack normally represents a distinct system you need to build, so separating the Terraform states for each part of your infrastructure makes sense. Features like cross-stack references and multi-stack deployments allow you to work with a variety of stacks at once and use values from different stacks. For example, the credentials from your cluster can be stored in one stack and accessed from another.
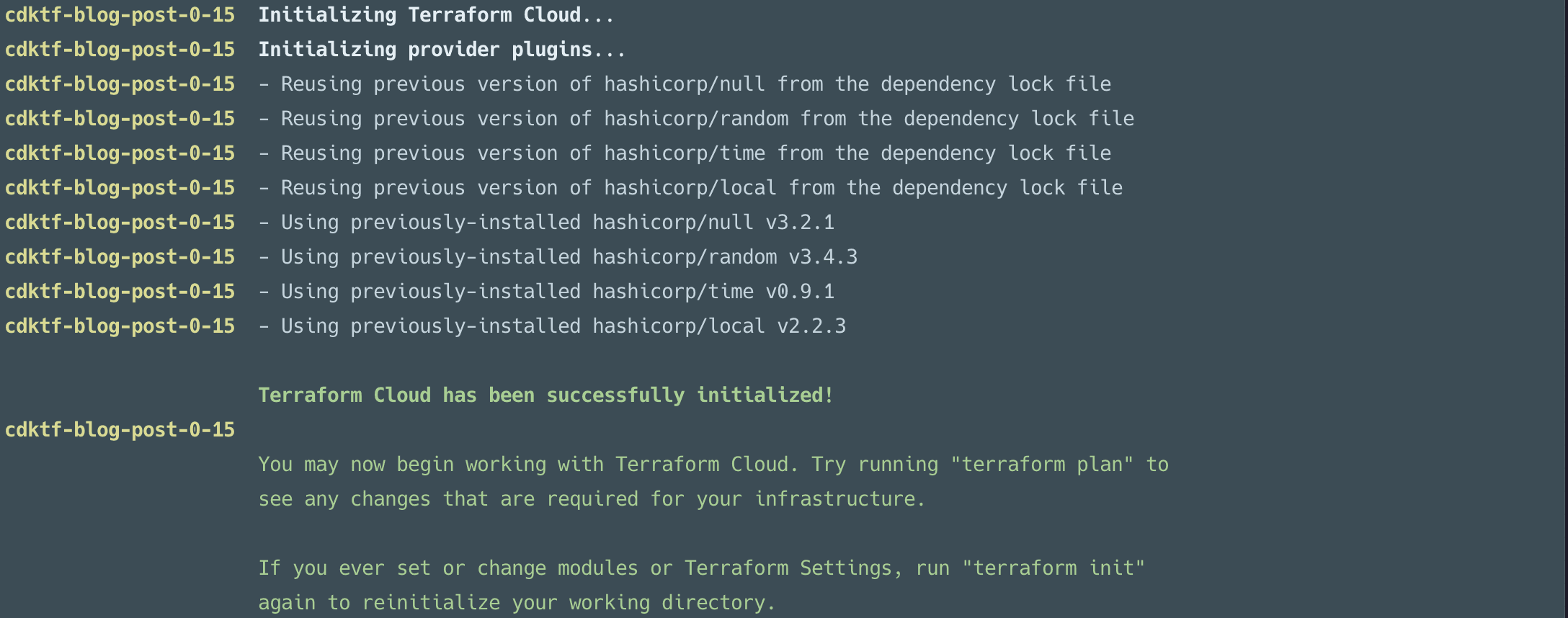
Even though adding a new Terraform stack in your application code is easy, earlier versions of CDKTF required you to go to the Terraform Cloud/Enterprise UI to create a new Terraform workspace every time. If you forgot to add a new workspace, you were likely to be greeted with an error like this:
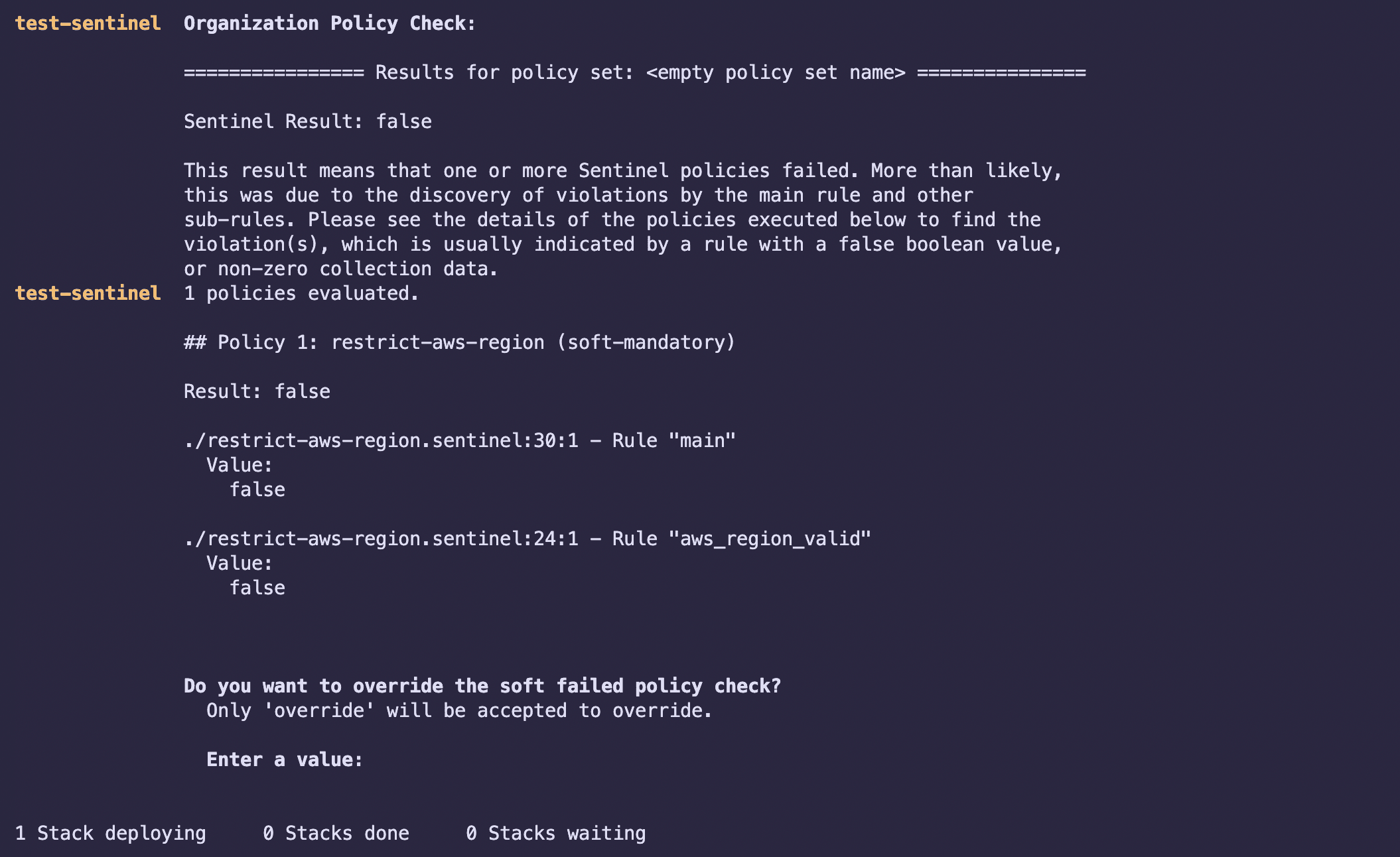
Beginning with the 0.15 release, CDKTF will automatically create the Terraform workspace for you. The first time you run plan and diff or apply and deploy on the new stack, CDKTF will use the CloudBackend you configured to create the Terraform workspace for you. No more context switching needed:
»Improve Parity with Terraform Cloud/Enterprise
CDKTF 0.15 also improves the user experience on a few Terraform Cloud and Terraform Enterprise edge cases: for example, when no Terraform agents were free or when your Terraform Enterprise installation had well-known endpoints. By replacing the API client with calls to Terraform, CDKTF now properly supports all Terraform Cloud and Terraform Enterprise edge cases. This also means that Sentinel policies are now fully supported.
»What's Next for CDKTF?
The upcoming CDKTF 0.16 release will focus on improving the cdktf convert command, which translates HashiCorp Configuration Language (HCL) into CDKTF syntax in your programming language of choice.
»Try CDK for Terraform
If you’re new to the project, these tutorials for CDK for Terraform are the best way to get started. You can dive deeper into our documentation with this overview of CDKTF.
Whether you’re still experimenting or actively using CDK for Terraform, we’d love to hear from you. Please file any bugs you encounter, let us know about your feature requests, and share your questions, thoughts, and experiences in the CDK for Terraform discussion forum.









