Kubernetes is a popular, open-source container orchestration tool adopted by many organizations. We created a collection of Terraform tutorials that can help you through your Kubernetes adoption journey.
»Provision a Kubernetes cluster
The first set of tutorials is designed to help you provision a Kubernetes cluster on popular cloud providers. These tutorials leverage both Terraform modules and resources to provision a functional cluster that you can connect to and interact with.
The Provision an EKS Cluster (AWS) tutorial will walk you through how to provision a Kubernetes cluster in AWS. In this tutorial, you will configure the AWS CLI to provide credentials to Terraform, clone an example repository, and deploy the cluster. Then, you will configure
kubectland deploy the Kubernetes dashboard and metrics server onto the newly provisioned cluster.The Provision an AKS Cluster (Azure) tutorial will walk you through how to provision a Kubernetes Cluster in Azure. In this tutorial, you will configure the Azure CLI to provide credentials to Terraform, clone an example repository, and deploy the cluster. Then you will configure
kubectlto interact with the newly provisioned cluster.The Provision a GKE Cluster (Google Cloud) tutorial will walk you through how to provision a Kubernetes cluster in Google Cloud Platform (GCP). In this tutorial, you will configure the gcloud SDK to provide credentials to Terraform, clone an example repo, and deploy the cluster. Then, you will configure
kubectland deploy the Kubernetes dashboard onto the newly provisioned cluster.
»Manage a Kubernetes cluster using Terraform
You can use the Terraform Kubernetes provider to manage your newly provisioned Kubernetes cluster (or an existing one).
In the Manage Kubernetes Resources via Terraform tutorial, you will schedule an NGINX instance and expose it using the Terraform Kubernetes Provider. Then, you will update the Terraform configuration to easily scale your NGINX deployment.
If you don’t have an existing Kubernetes cluster, we’ve also included instructions for kind, a tool for running local Kubernetes clusters using Docker containers.
»Deploy a Consul-backed Vault cluster on Kubernetes
In the last guide in our Kubernetes collection, Deploy Consul and Vault on Kubernetes with Run Triggers, you will create three Terraform Cloud workspaces to deploy a Consul-backed Vault cluster on a Kubernetes cluster hosted on Google Cloud.
The Kubernetes workspace will deploy a Kubernetes cluster on Google Cloud.
The Consul workspace will deploy a Consul on the Kubernetes cluster using a Helm chart
The Vault workspace will deploy Vault (configured to use Consul as a backend) on the Kubernetes cluster using a Helm chart
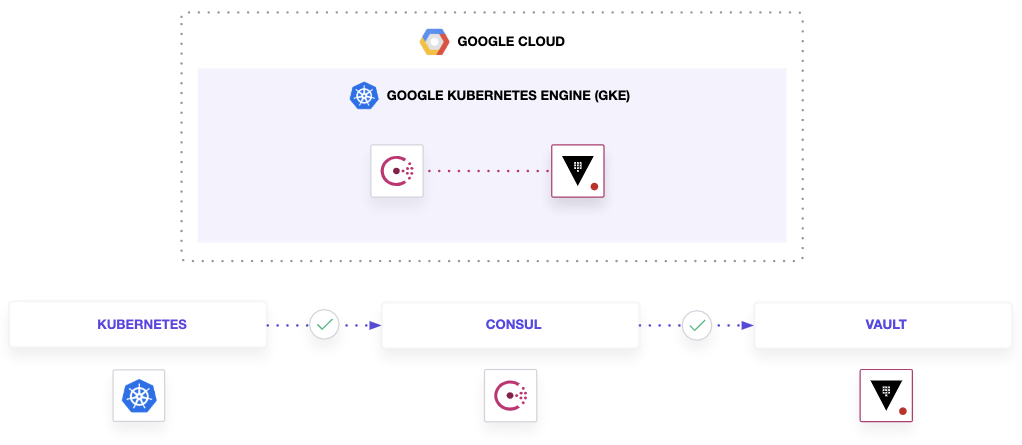
Since these workspaces are interdependent, you will be leveraging run triggers to automatically create run plans for downstream workspaces. In addition, you will learn how to share data between workspaces using output and terraform_remote_state.
This tutorial highlights Terraform and Terraform Cloud (TFC) best practices for code management and modules.









