Policies are rules that HashiCorp Terraform Cloud enforces at the Terraform run phase that can help with security, compliance, and cost management. Policies can be defined in Terraform Cloud using Sentinel and the Open Policy Agent (OPA) policy as code frameworks.
Today, we are excited to announce a new feature that addresses a critical challenge faced by customers in policy as code integration with Terraform Cloud: policy runtime version management; a new feature that enables users to select a specific Sentinel or OPA runtime version for their policy sets. This update introduces a policy runtime version pinning feature that provides Terraform Cloud users with more control, flexibility, and stability in their policy deployments.
Policy runtime version management enables users to select specific policy as code runtime versions in Terraform Cloud to reduce the impact of version conflicts, unexpected upgrades, and bugs, making policy enforcement more stable and efficient.
»Policy versioning challenges
Previously, Terraform Cloud users were required to use the most recent version of Sentinel or OPA, which inconvenienced customers who prefer to pin their policy set to a particular policy engine’s runtime version. This limitation could become problematic when new versions of Sentinel or OPA introduced language changes or syntax conflicts, resulting in broken policies and leading to provisioning failures and delays.
»Introducing policy runtime version management
Policy runtime version management provides increased control over policy as code versioning in Terraform Cloud. By default, Terraform Cloud will still use the latest Sentinel or OPA version, but users can now select specific runtime versions from a list of previously supported releases.
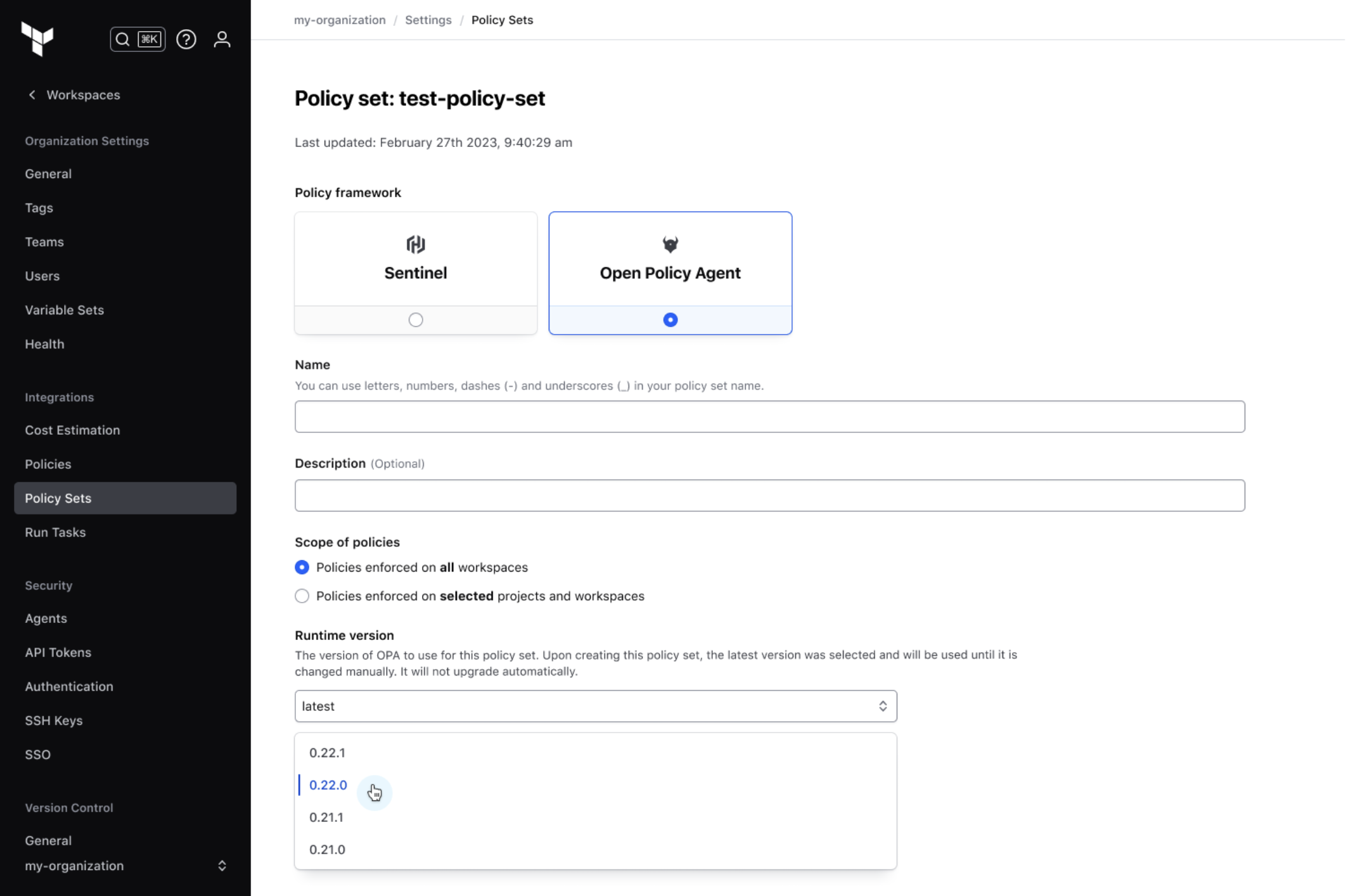
With policy runtime version management, Terraform Cloud users can select from a list of available runtime versions.
»Getting started with policy runtime version management
To start managing policy runtime versions in Terraform Cloud, check out the policy runtime documentation.
You can get started with Terraform Cloud for free to begin provisioning and managing your infrastructure in any environment. And don’t forget to link your Terraform Cloud and HashiCorp Cloud Platform (HCP) accounts together for a seamless sign-in experience.









