When we talk to customers about why they choose Terraform Cloud, they often aim to increase their provisioning velocity across their organization. However, provisioning doesn’t happen in a vacuum. Different business units like Finance, Security, and Compliance must ensure that their goals are met any time a change is introduced to infrastructure. This often necessitates a pass-off to other teams for code review, which will slow DevOps teams down.
Policy as code speeds up this review process by enabling organizations to define requirements from these teams as code, which enables automated testing and automated deployment. Our customers have generally defined policy as code using custom policies written in the HashiCorp policy as code framework, Sentinel. We’re now opening up the Terraform Cloud workflow to other third-party security and compliance tools with Run Tasks, which are now generally available.
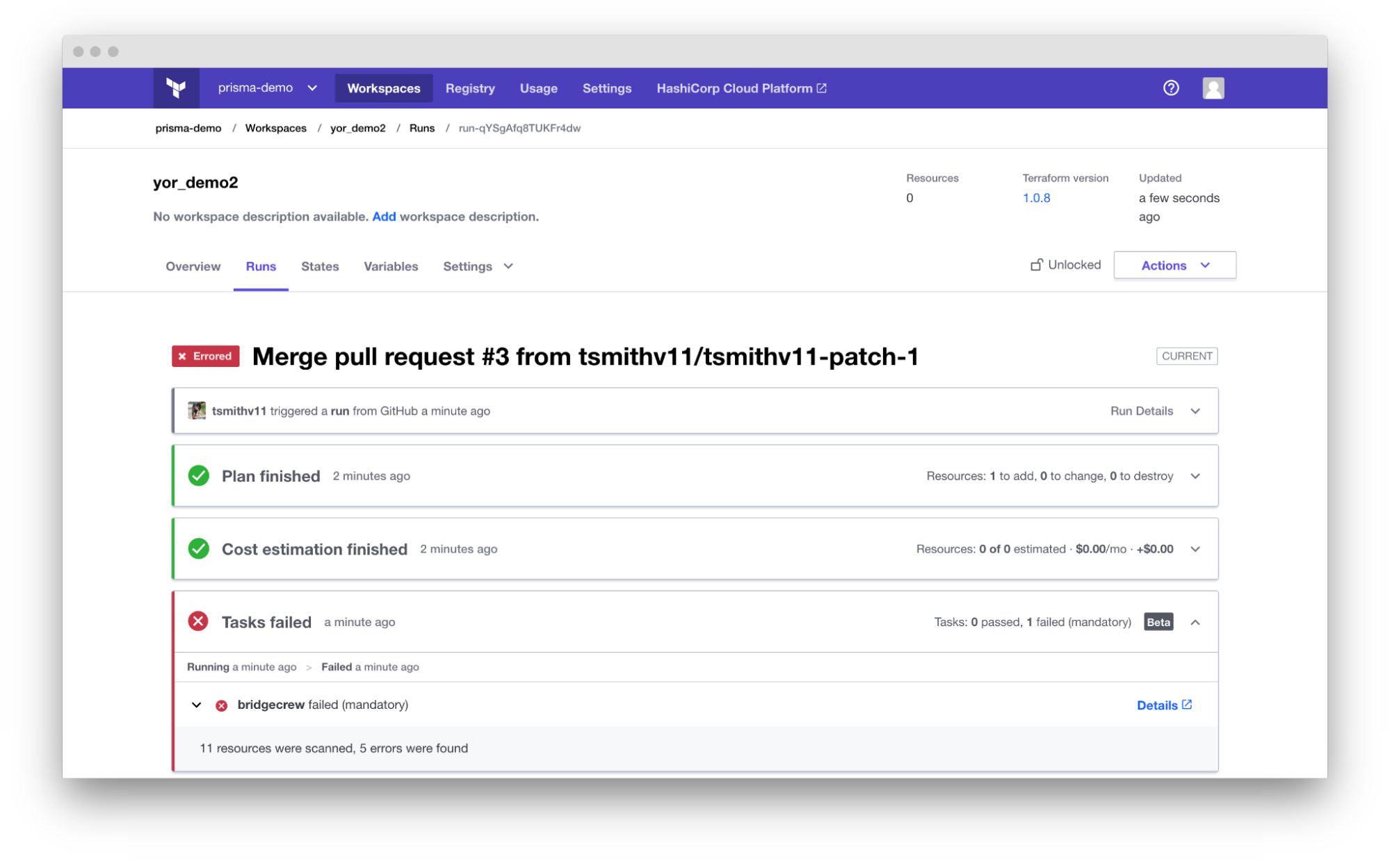
Figure: An example run task that runs code scans using Bridgecrew.
»Automate Code Review Using Third Party Tools
Your teams can integrate third-party tools into the Terraform Cloud workflow between any plan and apply. By opening up the workflow this way, you can set up conditions for runs to pass in minutes, all without having to write Sentinel policies yourself. This reduces manual code review and speeds up provisioning.
What are some use cases for post-plan run task integrations?
Security: Ensure that you’re not provisioning misconfigurations that cause security issues using tools like Snyk, Bridgecrew, Tenable, Moderne, Sophos, Aqua Security, Firefly, and Lightlytics
Cost control: Provide visibility into the costs of infrastructure prior to any change using Infracost, Vantage, or Kion
Regulatory compliance: Ensure compliance with various regulations like HIPAA, GDPR, or PCI-DSS with Bridgecrew or Kion
Run tasks now support a number of integrations, which you can find on this list If you don’t see a tool you’d like to use from this existing list, you can integrate it yourself.
»Available in the Terraform Cloud Business Tier; Coming Soon to Terraform Enterprise
Run task integrations will be in the Terraform Cloud Team & Governance as well as the Business tier, and are expected to be in a release of Terraform Enterprise very soon. This will also enable Terraform Enterprise customers to gain image compliance checks from HCP Packer. Contact our sales team if you are interested in setting up this integration.
»Getting Started with Run Tasks
Since releasing run tasks in beta, the Terraform Cloud team made these integrations easier than ever to set up in the UI or the API, ensuring your team can set up and test as many integrations as you’d like prior to committing them to your production workflows.
There are already many useful Terraform Cloud run task integrations available, and there will be more to come soon. Check out the documentation to see how to set up run task integrations via the UI or API, or get started quickly with this hands-on integration tutorial with Snyk.









