Earlier this year, during HashiConf Europe’s day one keynote, we previewed a new feature called Run Tasks for HashiCorp Terraform Cloud. The run tasks feature was built to allow you to integrate third-party tools directly into specific points during the Terraform Cloud workflow. Today, we are announcing the start of the beta period for Terraform Cloud run tasks for those who opted-in through our beta process. We have also turned this feature on for all existing Terraform Cloud Business tier customers. At the point of general availability, run tasks will be made available to organizations of all tiers.
»Integrate Third-Party Tools Into the Terraform Cloud Workflow
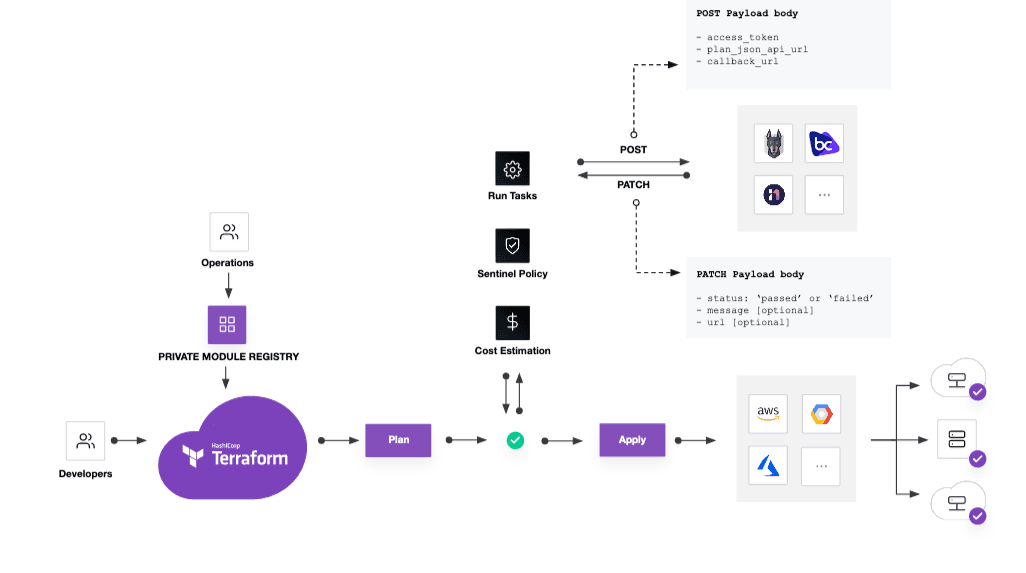
This beta feature enables your organization to integrate third-party tools within a Terraform run, specifically between the plan and apply stages of the Terraform Cloud workflow. Anything from security checks to cost estimation to code scanning can be integrated into your Terraform workflow with run tasks.
A run task works by sending run-related information to an external third-party system. At that point, the external system evaluates the information and returns a passed or failed response back to Terraform Cloud. The status response, combined with the task’s enforcement setting, determines whether a run should proceed to the next stage of the workflow.
We have worked with several technology partners to have pre-built integrations available for our customers at the beta launch.
»Bridgecrew
The integration with Bridgecrew helps teams address security and compliance errors in Terraform configurations as part of each and every code review.
»cloudtamer.io
cloudtamer.io has two integration options: Customers can choose to focus on cost savings or compliance findings on an active account when using cloudtamer.io.
»Infracost
Infracost allows cloud infrastructure costing, initiated right from a pull request or Terraform run.
»Lightlytics
Lightlytics enables full Terraform impact analysis before deployment, see the potential impact of every proposed change on your entire cloud posture and services, eliminate availability and security issues before production
»Refactr
Refactr’s integration allows users to build workflows for multiple use cases including but not limited to code scanning.
»Snyk
Snyk’s integration allows teams using Terraform to find, track, and fix security misconfigurations in their cloud infrastructure as part of their SDLC before they ever reach production.
These are the first of many integrations we plan to be adding soon, and an up-to-date list can be found here.
»Get Started with Run Tasks
There are no specific limits on how run tasks can be used, and the feature is open for anyone to develop against; no formal approval process is required. Documentation on how to build your own integrations is available here.
Terraform Cloud is free to try, and organizations can upgrade to the Team & Governance or Business tiers at any time. To get started, sign up for Terraform Cloud and follow our Get Started tutorial. To get started with run tasks, contact HashiCorp Sales to upgrade to the Business tier, and reference the run tasks documentation.










