We are excited to announce Drift Detection for Terraform Cloud, now in public beta for HashiCorp Terraform Cloud Business. Drift Detection provides continuous checks against infrastructure state to detect and notify when there are changes.
This new feature continues to evolve the capabilities in HashiCorp Terraform to provide operators with continuous visibility into the state of their multi-cloud infrastructure. Drift Detection follows the announcements of Terraform 1.2 and Terraform Run Tasks, which are additional capabilities that increase efficiency while reducing risk related to security, compliance, and operational consistency. The new capabilities expand Terraform’s support for “Day 2” operations for cloud infrastructure.
As organizations migrate to the cloud, they need infrastructure automation to efficiently provision and manage their cloud resources. Typically, that consists of three distinct phases: Adopting and establishing a provisioning workflow, standardizing the workflow, and operating and optimizing at scale across multi-cloud environments as well as private datacenters. Infrastructure as code — along with proper guardrails — are essential to this process. Terraform helps organizations with infrastructure automation and provides capabilities across all three of these phases.
»Challenges in Maintaining Accurate Infrastructure State
Reliance on a standardized provisioning workflow requires that your teams have confidence in the recorded state of the infrastructure. The challenge is that once infrastructure is provisioned, how do you ensure the actual state of infrastructure reflects the known and recorded infrastructure state? Despite everyone's best efforts, multiple provisioning workflows, developers, and infrastructure access points mean that infrastructure will frequently be changed and updated to a point where the infrastructure state changes may not match the state defined in the code — a phenomenon called configuration drift.
Drift can cause problems in several ways. For example, development teams unaware of production environment changes may see applications suddenly crash and deployment projects unexpectedly fail because they couldn’t see all the changes that had actually been made by looking at the infrastructure code. Without a single, shared source of truth, intentional infrastructure changes to remediate incidents could be reverted or temporary changes left unnoticed, wasting thousands of dollars in monthly costs due to unused resources. Drift can also lead to serious security issues, as mission-critical systems may be unwittingly left open to public access and unknown resources may be left unsecured. (See HashiCorp CISO Talha Tariq’s perspective on the security risks of undetected drift on The New Stack: How Drift Detection and IaC Help Maintain a Secure Infrastructure.)
But manually tracking infrastructure changes and then restoring to correct state or updating configurations to match current infrastructure is time-consuming and impossible to scale. If infrastructure changes occur, they must be detected and notifications or alerts must be sent so operators can correct the drift.
»Introducing Drift Detection for Terraform
To solve this problem, Drift Detection for Terraform provides built-in continuous checks against infrastructure state to detect changes and provide alerts. This allows Terraform to provide a central pane of visibility to all your infrastructure and offers operators confidence that it matches the last known Terraform state.
»Drift Detection
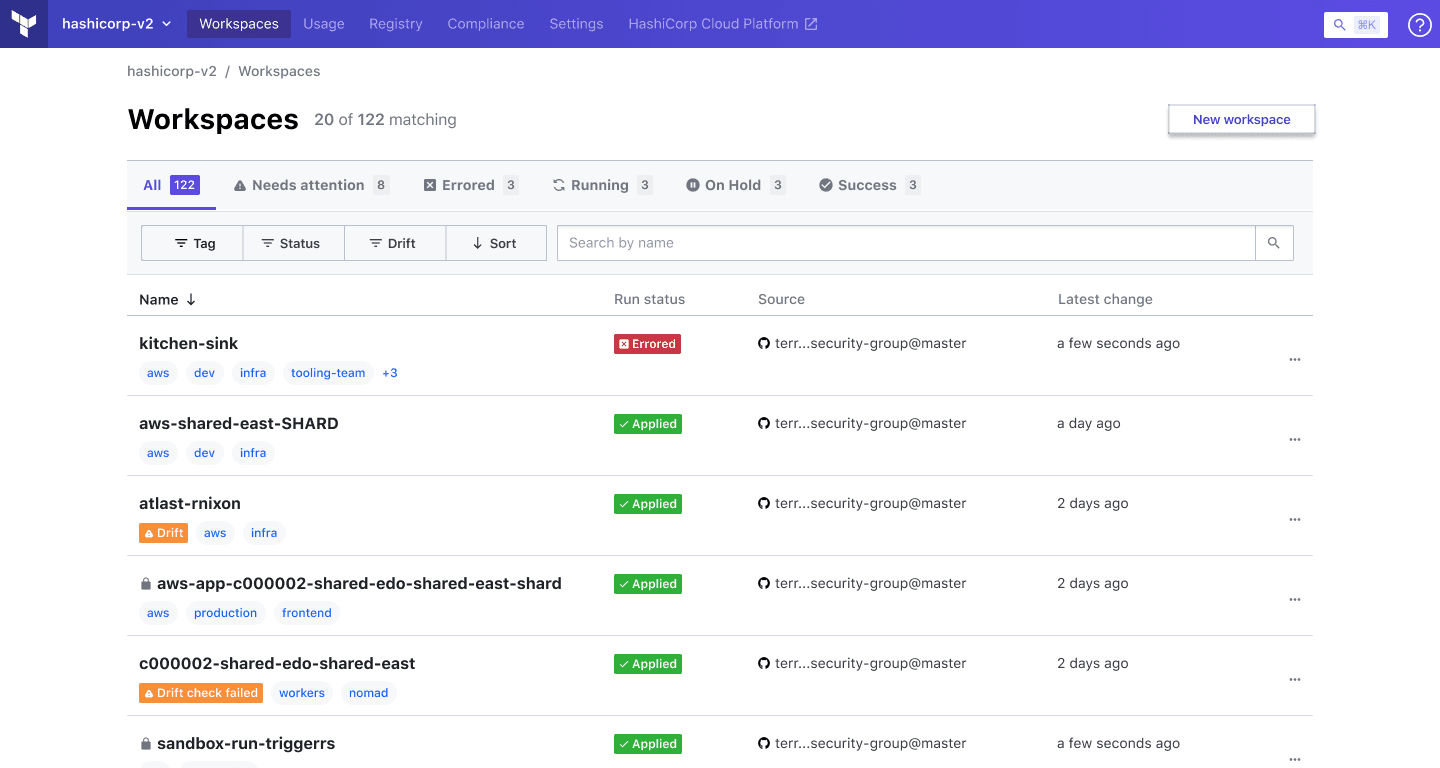
Terraform Drift Detection preemptively detects when a resource has changed from what Terraform has reflected in the state file. The workspaces view includes a new Drift designation in the workspace index listing, as well as a filter for drift.
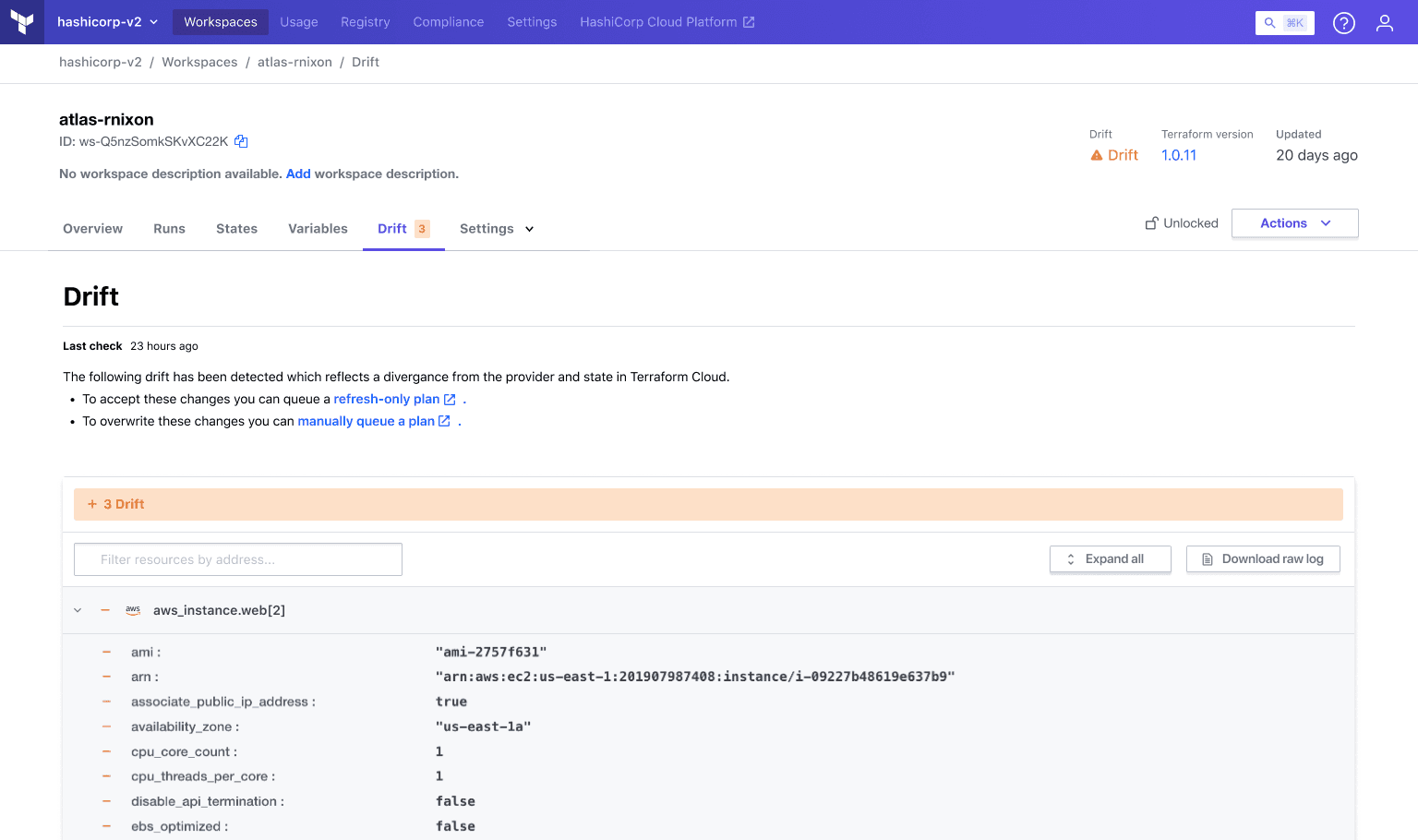
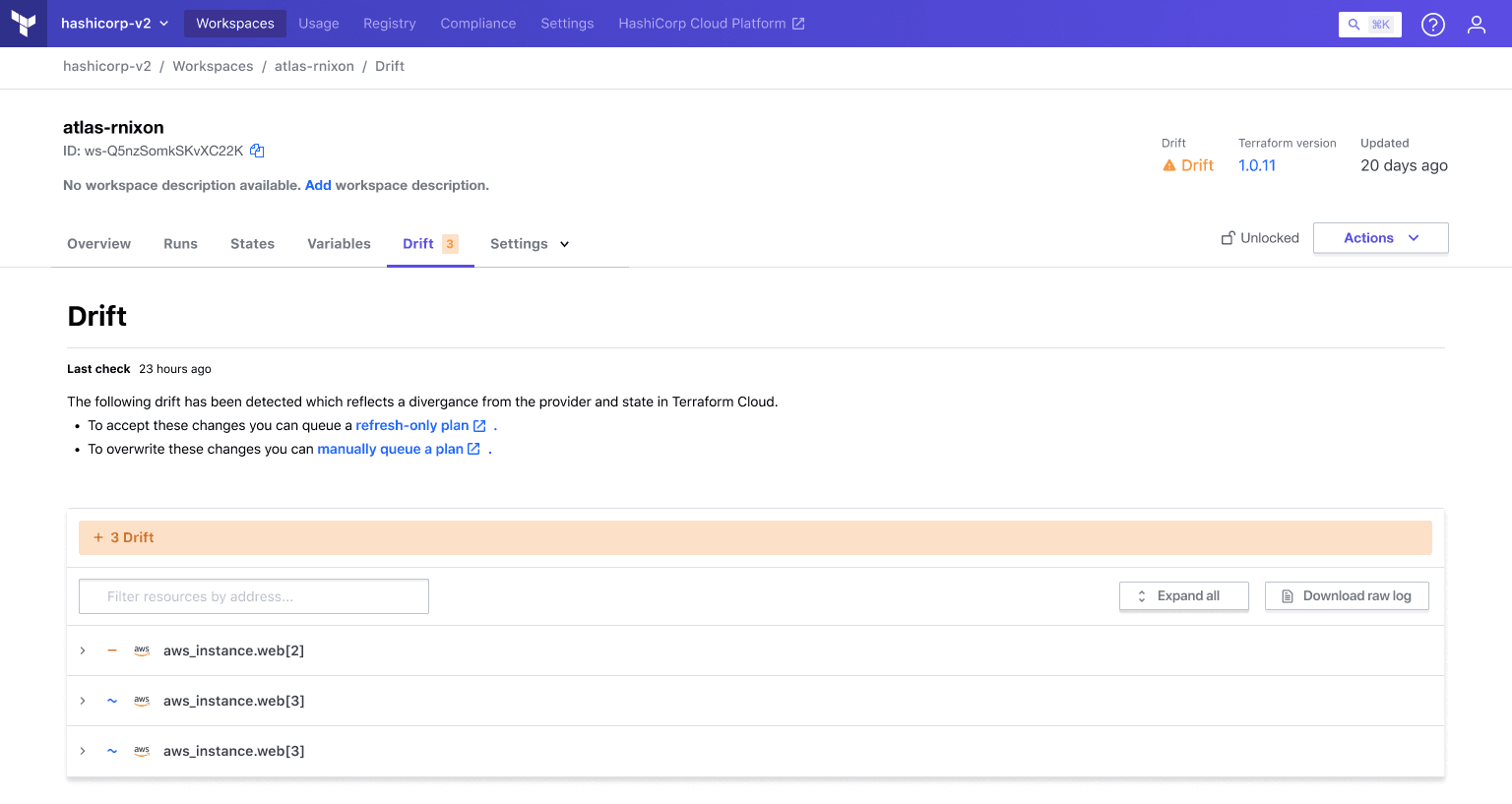
Each workspace where Drift Detection has been enabled displays the current state of drift as a top-level item, alongside Terraform version, resource count, and the time of the last update.
Workspaces also features a new Drift tab. The tab itself highlights the number of resources currently in a state of drift. Clicking into the tab provides additional information such as:
- The last time drift was checked
- The resources detected as being in a state of drift
- A visualization showing which attributes have changed
»Drift Notification
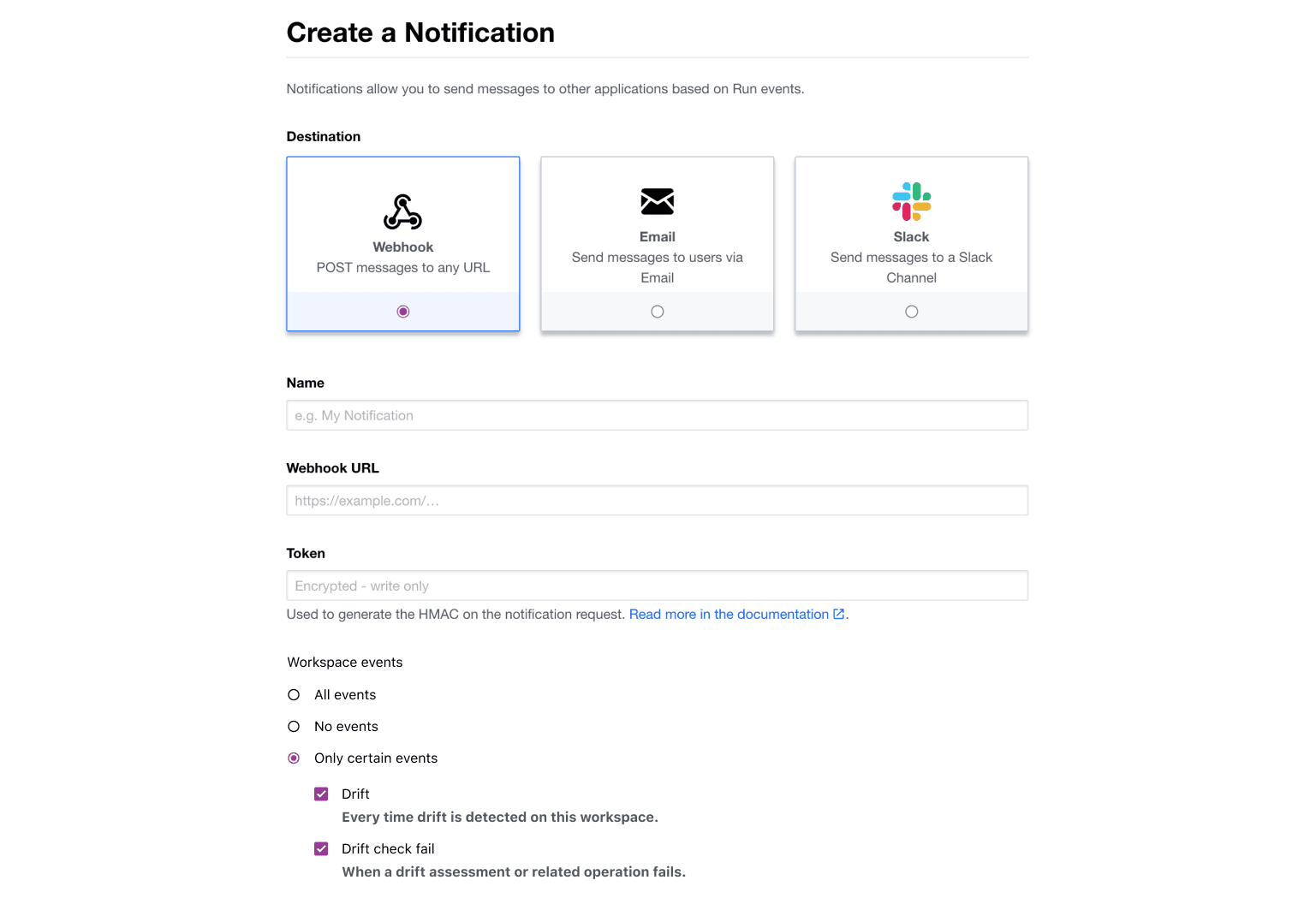
If infrastructure drift occurs, operators need to be informed as quickly as possible. With Drift Detection for Terraform Cloud you can create customizable notifications to make sure the right people are alerted using your preferred method of communication, whether that’s via email, Slack, or a webhook.
»Drift Remediation
Detection of drift is only the first step — the drift must also be remediated. Operators can resolve drift issues directly from the Terraform Drift tab by accepting changes with a refresh-only plan or by making changes to the new infrastructure state.
»Benefits of Built-in Drift Detection
Awareness of drift helps ensure that all your infrastructure is governed and has the proper security measures in place. It also reduces the potential for application downtime that could negatively impact the user experience and, eventually, revenue. Automatic, customizable notifications to the appropriate people so they can see and understand infrastructure changes not reflected in the code is essential to avoiding unnecessary problems and costs.
Built-in drift detection in Terraform Cloud fosters increased organizational agility by offering a central plane to manage and provide visibility into your infrastructure without manual intervention or having to add and learn new tools.
»Summary
To fully reap the benefits of infrastructure as code, operators must be able to detect changes in the infrastructure state not reflected in the code. Drift Detection for Terraform Cloud provides continuous checks against infrastructure state to detect and notify operators of changes in your infrastructure to minimize your risk exposure, application downtime, and costs. HashiCorp Terraform already provides a provisioning workflow and infrastructure lifecycle management capabilities, and Drift Detection further enhances Terraform’s ability to help organizations standardize their workflows.
To learn more about Drift Detection for Terraform Cloud, watch the demo video below or check out our new Drift Detection page. Sign up for Terraform Cloud to get started for free to provision, change, and version infrastructure resources on any environment.








